-
Beta Was this translation helpful? Give feedback.
Replies: 2 comments 6 replies
-
|
Wait do you have a typo ? {
name: 'Bravo'
port: 456
domain: ''
}did you try or should I say ... did you try |
Beta Was this translation helpful? Give feedback.
-
|
Sorry about the slow reply - been out sick for a few days. Not a typo - if a domain isn't provided to an Application Gateway rule, it matches to all of them (according to support), so it's intended to be more of a catch-all fallback rule. Implementation of my idea or any of the linked issues there would be really useful in accomplishing this without resorting to PowerShell scripts (especially since I've since found a bug in how ARM handles lists in those recently). I ultimately solved this in a different way and was pleasantly surprised that it worked. From my resource group template: //root.bicep
var certificateSubjects = [
{
subjectName: '*.abc.com'
targetNodeTypes: [
'web'
'processing'
]
}
{
subjectName: '*.def.com'
targetNodeTypes: [
'web'
]
}
{
}
]
module Deployment 'resourceGroup.bicep' = [for dp in deployments: {
//...
params: {
CertificateSubjects: certificateSubjects
}
}]// resourceGroup.bicep
//Deploy each of the wildcard certificates
@batchSize(1)
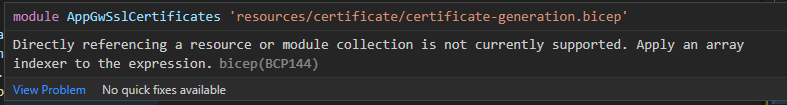
module SslCertificates './resources/certificate/certificate-generation.bicep' = [for (certificate, index) in CertificateSubjects: {
name: take('${resourceMapping['deployment']}-${DeploymentPrefix}-${resourceMapping['certificateIssue']}-${replace(certificate.subjectName, '*', 'wild')}', 64)
params: {
Domain: certificate.subjectName
Location: Location
}
}]
module AppGw './appGw.bicep' {
//...
params: {
CertificateSubjects: certificateSubjects
}
}//appGw.bicep
resource Certificate 'Microsoft.KeyVault/vaults/secrets@2021-11-01-preview' existing = [for cert in CertificateSubjects: {
name: replace(replace(cert.subjectName, '*', 'wild'), '.', '-')
}]
resource AppGw 'Microsoft.Network/applicationGateways@2021-05-01' = {
name: 'abcdef'
properties: {
//...
sslCertificates: [for (cert, index) in CertificateSubjects: {
name: '${replace(replace(cert.subjectName, '.', '-'}, '*', 'wild')}-${UtcNow}'
properties: {
keyVaultSecretId: Certificate[index].properties.secretUri
}
}]
}
}This whole thing works simply because of the existing resource lookup there at the very end, but at least it works with a bit of a variable redesign. Thanks for the ideas though! |
Beta Was this translation helpful? Give feedback.
Sorry about the slow reply - been out sick for a few days.
Not a typo - if a domain isn't provided to an Application Gateway rule, it matches to all of them (according to support), so it's intended to be more of a catch-all fallback rule.
Implementation of my idea or any of the linked issues there would be really useful in accomplishing this without resorting to PowerShell scripts (especially since I've since found a bug in how ARM handles lists in those recently).
I ultimately solved this in a different way and was pleasantly surprised that it worked. From my resource group template: