Click to expand
+Vulnerability Log
-```json title="Vulnerability Log" +```json { "id": "d5bde2e631d14103970a27924943a07c_9e90a7c915043320bbfc1534f438a60c", "cid": "2ae7654232b94d7c99305e5bc5484ed1", @@ -393,17 +393,37 @@ _sourceCategory="Labs/CrowdstrikeSpotlight" ``` -## Set up collection +## Collection configuration and app installation -To set up the [CrowdStrike Spotlight Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/crowdstrike-spotlight-source) for the CrowdStrike Spotlight app, follow the instructions provided. These instructions will guide you through the process of creating a source using the CrowdStrike Spotlight Source category, which you will need to use when installing the app. By following these steps, you can ensure that your CrowdStrike Spotlight app is properly integrated and configured to collect and analyze your CrowdStrike Spotlight data. +Depending on the set up collection method, you can configure and install the app in three ways: -## Installing the CrowdStrike Spotlight app +- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or +- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or +- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app. -import AppInstall2 from '../../reuse/apps/app-install-v2.md'; +:::important +Use the [Cloud-to-Cloud Integration for CrowdStrike Spotlight](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/crowdstrike-spotlight-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your CrowdStrike Spotlight app is properly integrated and configured to collect and analyze your CrowdStrike Spotlight data. +::: + +### Create a new collector and install the app + +import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md'; + +
+
+
+Sample Phishing Security Tests Log
+ +```json { "campaign_id": 1892087, "pst_id": 8805725, @@ -65,8 +68,12 @@ The Sumo Logic App for KnowBe4 consumes Phishing Security logs. Refer to the [Kn "bounced_count": 0 } ``` +
+
## Sample queries
@@ -122,15 +129,37 @@ email, scheduled_at, delivered_at, opened_at, clicked_at, replied_at, attachment
| count_distinct(recipient_id)
```
-## Installing the KnowBe4 App
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for KnowBe4](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/proofpoint-tap-source/) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your KnowBe4 app is properly integrated and configured to collect and analyze your KnowBe4 data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+Sample Recipient Results Log
-```json title="Sample Recipient Results Log" +```json { "recipient_id": 1498372653, "pst_id": 8805725, @@ -101,7 +108,7 @@ The Sumo Logic App for KnowBe4 consumes Phishing Security logs. Refer to the [Kn "os": "mac" } ``` - +}) diff --git a/docs/integrations/saas-cloud/lastpass.md b/docs/integrations/saas-cloud/lastpass.md
index d145b61782..30fe0d0360 100644
--- a/docs/integrations/saas-cloud/lastpass.md
+++ b/docs/integrations/saas-cloud/lastpass.md
@@ -46,17 +46,37 @@ _sourceCategory="lastpass_event" Action Username
| limit 10
```
-## Set up collection
+## Collection configuration and app installation
-To set up the [LastPass Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/lastpass-source) for the LastPass app, follow the instructions provided. These instructions will guide you through the process of creating a source using the LastPass Source category, which you will need to use when installing the app. By following these steps, you can ensure that your LastPass app is properly integrated and configured to collect and analyze your LastPass data.
+Depending on the set up collection method, you can configure and install the app in three ways:
-## Installing the LastPass app
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
-import AppInstall2 from '../../reuse/apps/app-install-v2.md';
+:::important
+Use the [Cloud-to-Cloud Integration for LastPass](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/lastpass-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your LastPass app is properly integrated and configured to collect and analyze your LastPass data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+
diff --git a/docs/integrations/saas-cloud/lastpass.md b/docs/integrations/saas-cloud/lastpass.md
index d145b61782..30fe0d0360 100644
--- a/docs/integrations/saas-cloud/lastpass.md
+++ b/docs/integrations/saas-cloud/lastpass.md
@@ -46,17 +46,37 @@ _sourceCategory="lastpass_event" Action Username
| limit 10
```
-## Set up collection
+## Collection configuration and app installation
-To set up the [LastPass Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/lastpass-source) for the LastPass app, follow the instructions provided. These instructions will guide you through the process of creating a source using the LastPass Source category, which you will need to use when installing the app. By following these steps, you can ensure that your LastPass app is properly integrated and configured to collect and analyze your LastPass data.
+Depending on the set up collection method, you can configure and install the app in three ways:
-## Installing the LastPass app
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
-import AppInstall2 from '../../reuse/apps/app-install-v2.md';
+:::important
+Use the [Cloud-to-Cloud Integration for LastPass](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/lastpass-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your LastPass app is properly integrated and configured to collect and analyze your LastPass data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+
+
+
+Users
+ +```json { "businessPhones": [ "800-555-0101" @@ -46,8 +49,12 @@ This app uses Sumo Logic’s Microsoft Azure AD Inventory Source to collect [Use } } ``` +
+
### Sample queries
@@ -126,17 +134,37 @@ _sourceCategory="Azure_AD_Inventory" deviceId
| count
```
-## Set up collection
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for Microsoft Azure AD Inventory](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-azure-ad-inventory-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Microsoft Azure AD Inventory app is properly integrated and configured to collect and analyze your Microsoft Azure AD Inventory data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+Devices
-```json title="Devices" +```json { "id": "3344aabb-ccdd-eeff-8899-1234567890ab", "deletedDateTime": null, @@ -108,6 +115,7 @@ This app uses Sumo Logic’s Microsoft Azure AD Inventory Source to collect [Use ] } ``` +
-
+
+View Sample Log Message
+Audit Activity Message
-```json title="Audit Activity Message" +```json { "id": "Directory_d4d04864-b03e-4a15-9899-cb36abd1e7d2_CYJZP_45515702", "category": "ApplicationManagement", @@ -79,7 +79,12 @@ The App uses Microsoft Graph Azure AD Reporting Source to collect [Audit](https: ] } ``` -```json title="Sign-In Activity" +
+
+
+Sign-In Activity
+ +```json { "id": "66ea54eb-6301-4ee5-be62-ff5a759100", "createdDateTime": "2023-05-09T11:41:56.7381342Z", @@ -145,8 +150,12 @@ The App uses Microsoft Graph Azure AD Reporting Source to collect [Audit](https: ] } ``` +
+
-## Set up collection
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for Microsoft Graph Azure AD Reporting](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-azure-ad-reporting-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Microsoft Graph Azure AD Reporting app is properly integrated and configured to collect and analyze your Microsoft Graph Azure AD Reporting data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+Provisioning Activity
-```json title="Provisioning Activity" +```json { "id": "75b5b0ae-9fc5-8d0e-e0a9-7y6a4728de56", "activityDateTime": "2019-05-09T03:00:54Z", @@ -289,17 +298,35 @@ _sourceCategory="azure_ad_reporting" "provisioningAction" "provisioningSteps" "p ```}) +The **Microsoft Graph Azure AD Reporting - Audits** dashboard enables you to analyze the distribution of audit activities across resource categories, audit operations, and audit services. You can also view the distribution of user agents that perform audits and target resource types. This dashboard also highlights the most common reasons for activity failures. Additionally, it presents a summary of recent audit activities. Altogether this dashboard provides valuable insights into your organization's audit activity data.
+The **Microsoft Graph Azure AD Reporting - Audits** dashboard enables you to analyze the distribution of audit activities across resource categories, audit operations, and audit services. You can also view the distribution of user agents that perform audits and target resource types. This dashboard also highlights the most common reasons for activity failures. Additionally, it presents a summary of recent audit activities. Altogether this dashboard provides valuable insights into your organization's audit activity data.}) -### Microsoft Graph Azure AD Reporting - Sign-Ins
+### Sign-Ins
-**Microsoft Graph Azure AD Reporting - Sign-Ins** dashboard provides valuable insights into your organization's sign-in activity data over time. It displays the geographical locations of sign-in activities, including those from high-risk countries. You can also see the distribution of interactive users and the client apps used for sign-in activities. The dashboard also highlights the most frequently accessed resources. Risk analysis is provided by showing the distribution of risk states, risk levels, and risk event types. Additionally, the reasons for risk detection are displayed. The dashboard also provides visibility into recent sign-in activities, making it a useful tool for monitoring and managing your organization's security posture.
-### Microsoft Graph Azure AD Reporting - Sign-Ins
+### Sign-Ins
-**Microsoft Graph Azure AD Reporting - Sign-Ins** dashboard provides valuable insights into your organization's sign-in activity data over time. It displays the geographical locations of sign-in activities, including those from high-risk countries. You can also see the distribution of interactive users and the client apps used for sign-in activities. The dashboard also highlights the most frequently accessed resources. Risk analysis is provided by showing the distribution of risk states, risk levels, and risk event types. Additionally, the reasons for risk detection are displayed. The dashboard also provides visibility into recent sign-in activities, making it a useful tool for monitoring and managing your organization's security posture.}) +The **Microsoft Graph Azure AD Reporting - Sign-Ins** dashboard provides valuable insights into your organization's sign-in activity data over time. It displays the geographical locations of sign-in activities, including those from high-risk countries. You can also see the distribution of interactive users and the client apps used for sign-in activities. The dashboard also highlights the most frequently accessed resources. Risk analysis is provided by showing the distribution of risk states, risk levels, and risk event types. Additionally, the reasons for risk detection are displayed. The dashboard also provides visibility into recent sign-in activities, making it a useful tool for monitoring and managing your organization's security posture.
+The **Microsoft Graph Azure AD Reporting - Sign-Ins** dashboard provides valuable insights into your organization's sign-in activity data over time. It displays the geographical locations of sign-in activities, including those from high-risk countries. You can also see the distribution of interactive users and the client apps used for sign-in activities. The dashboard also highlights the most frequently accessed resources. Risk analysis is provided by showing the distribution of risk states, risk levels, and risk event types. Additionally, the reasons for risk detection are displayed. The dashboard also provides visibility into recent sign-in activities, making it a useful tool for monitoring and managing your organization's security posture.}) -### Microsoft Graph Azure AD Reporting - Provisioning Activities
+### Provisioning Activities
-**Microsoft Graph Azure AD Reporting - Provisioning Activities** dashboard provides valuable insights into all provisioning activities occurring in your account. It displays the average time for each provisioning activity and provides a distribution of provisioning activities by status, actions, and initiators. Additionally, you can view the most frequently used service principal during provisioning. The dashboard also gives you visibility into recent provisioning activities, making it a useful tool for monitoring and managing your organization's provisioning processes.
-### Microsoft Graph Azure AD Reporting - Provisioning Activities
+### Provisioning Activities
-**Microsoft Graph Azure AD Reporting - Provisioning Activities** dashboard provides valuable insights into all provisioning activities occurring in your account. It displays the average time for each provisioning activity and provides a distribution of provisioning activities by status, actions, and initiators. Additionally, you can view the most frequently used service principal during provisioning. The dashboard also gives you visibility into recent provisioning activities, making it a useful tool for monitoring and managing your organization's provisioning processes.}) +The **Microsoft Graph Azure AD Reporting - Provisioning Activities** dashboard provides valuable insights into all provisioning activities occurring in your account. It displays the average time for each provisioning activity and provides a distribution of provisioning activities by status, actions, and initiators. Additionally, you can view the most frequently used service principal during provisioning. The dashboard also gives you visibility into recent provisioning activities, making it a useful tool for monitoring and managing your organization's provisioning processes.
+The **Microsoft Graph Azure AD Reporting - Provisioning Activities** dashboard provides valuable insights into all provisioning activities occurring in your account. It displays the average time for each provisioning activity and provides a distribution of provisioning activities by status, actions, and initiators. Additionally, you can view the most frequently used service principal during provisioning. The dashboard also gives you visibility into recent provisioning activities, making it a useful tool for monitoring and managing your organization's provisioning processes.}) ## Upgrade/Downgrade the Microsoft Graph Azure AD Reporting app (Optional)
diff --git a/docs/integrations/saas-cloud/microsoft-graph-security-v1.md b/docs/integrations/saas-cloud/microsoft-graph-security-v1.md
index 0f1944d8d4..43c20845be 100644
--- a/docs/integrations/saas-cloud/microsoft-graph-security-v1.md
+++ b/docs/integrations/saas-cloud/microsoft-graph-security-v1.md
@@ -9,10 +9,10 @@ import useBaseUrl from '@docusaurus/useBaseUrl';
## Upgrade/Downgrade the Microsoft Graph Azure AD Reporting app (Optional)
diff --git a/docs/integrations/saas-cloud/microsoft-graph-security-v1.md b/docs/integrations/saas-cloud/microsoft-graph-security-v1.md
index 0f1944d8d4..43c20845be 100644
--- a/docs/integrations/saas-cloud/microsoft-graph-security-v1.md
+++ b/docs/integrations/saas-cloud/microsoft-graph-security-v1.md
@@ -9,10 +9,10 @@ import useBaseUrl from '@docusaurus/useBaseUrl';
}) -The Sumo Logic App for Microsoft Graph Security V1 enables you to identify security threats by analyzing alert logs and helps you to improve web security posture, proactively detect and mitigate potential security risks, and improve compliance with security policies and regulations.
+The Sumo Logic app for Microsoft Graph Security V1 enables you to identify security threats by analyzing alert logs and helps you to improve web security posture, proactively detect and mitigate potential security risks, and improve compliance with security policies and regulations.
:::warning
-This version of the app uses alerts from Microsoft Graph API (https://learn.microsoft.com/en-us/graph/api/alert-list?view=graph-rest-1.0&tabs=http) and continues to be supported for existing customers who are bringing in alerts from that source. If you are setting up a new cloud-to-cloud source, it will use API V2 (https://learn.microsoft.com/en-us/graph/api/security-list-alerts_v2?view=graph-rest-1.0&tabs=http) which is covered by the [Microsoft Graph Security V2 app](/docs/integrations/saas-cloud/microsoft-graph-security-v2).
+This version of the app uses alerts from [Microsoft Graph API](https://learn.microsoft.com/en-us/graph/api/alert-list?view=graph-rest-1.0&tabs=http) and continues to be supported for existing customers who are bringing in alerts from that source. If you are setting up a new cloud-to-cloud source, it will use [API V2](https://learn.microsoft.com/en-us/graph/api/security-list-alerts_v2?view=graph-rest-1.0&tabs=http) which is covered by the [Microsoft Graph Security V2 app](/docs/integrations/saas-cloud/microsoft-graph-security-v2).
:::
Key features of the Microsoft Graph Security app include:
@@ -31,7 +31,10 @@ Learn more about [fields of alert](https://learn.microsoft.com/en-us/graph/api/r
## Sample log messages
-```json title="Sample Alert Log"
+
-The Sumo Logic App for Microsoft Graph Security V1 enables you to identify security threats by analyzing alert logs and helps you to improve web security posture, proactively detect and mitigate potential security risks, and improve compliance with security policies and regulations.
+The Sumo Logic app for Microsoft Graph Security V1 enables you to identify security threats by analyzing alert logs and helps you to improve web security posture, proactively detect and mitigate potential security risks, and improve compliance with security policies and regulations.
:::warning
-This version of the app uses alerts from Microsoft Graph API (https://learn.microsoft.com/en-us/graph/api/alert-list?view=graph-rest-1.0&tabs=http) and continues to be supported for existing customers who are bringing in alerts from that source. If you are setting up a new cloud-to-cloud source, it will use API V2 (https://learn.microsoft.com/en-us/graph/api/security-list-alerts_v2?view=graph-rest-1.0&tabs=http) which is covered by the [Microsoft Graph Security V2 app](/docs/integrations/saas-cloud/microsoft-graph-security-v2).
+This version of the app uses alerts from [Microsoft Graph API](https://learn.microsoft.com/en-us/graph/api/alert-list?view=graph-rest-1.0&tabs=http) and continues to be supported for existing customers who are bringing in alerts from that source. If you are setting up a new cloud-to-cloud source, it will use [API V2](https://learn.microsoft.com/en-us/graph/api/security-list-alerts_v2?view=graph-rest-1.0&tabs=http) which is covered by the [Microsoft Graph Security V2 app](/docs/integrations/saas-cloud/microsoft-graph-security-v2).
:::
Key features of the Microsoft Graph Security app include:
@@ -31,7 +31,10 @@ Learn more about [fields of alert](https://learn.microsoft.com/en-us/graph/api/r
## Sample log messages
-```json title="Sample Alert Log"
+
+
## Sample queries
@@ -115,23 +119,41 @@ _sourceCategory="ms_graph"
| count_distinct(alert_id)
```
-## Set up collection
+## Collection configuration and app installation
-Follow the instructions for setting up the [Cloud-to-Cloud Integration for Microsoft Graph Security](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-security-api-source/) source and use the same source category while installing the app.
+Depending on the set up collection method, you can configure and install the app in three ways:
-## Installing the Microsoft Graph Security app
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
-This section has instructions for installing the Microsoft Graph Security app for Sumo Logic.
+:::important
+Use the [Cloud-to-Cloud Integration for Microsoft Graph Security](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-security-api-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Microsoft Graph Security app is properly integrated and configured to collect and analyze your Microsoft Graph Security data.
+:::
-import AppInstall2 from '../../reuse/apps/app-install-v2.md';
+### Create a new collector and install the app
-Sample Alert Log
+ +```json { "azureSubscriptionId": null, "riskScore": null, @@ -104,6 +107,7 @@ Learn more about [fields of alert](https://learn.microsoft.com/en-us/graph/api/r "vulnerabilityStates": [] } ``` +}) -## Uninstalling the Microsoft Graph Security app (Optional)
+## Upgrade/Downgrade the Microsoft Graph Security app (Optional)
-import AppUninstall from '../../reuse/apps/app-uninstall.md';
+import AppUpdate from '../../reuse/apps/app-update.md';
-
-## Uninstalling the Microsoft Graph Security app (Optional)
+## Upgrade/Downgrade the Microsoft Graph Security app (Optional)
-import AppUninstall from '../../reuse/apps/app-uninstall.md';
+import AppUpdate from '../../reuse/apps/app-update.md';
-
- -### Microsoft Graph Security - Alerts Security Overview
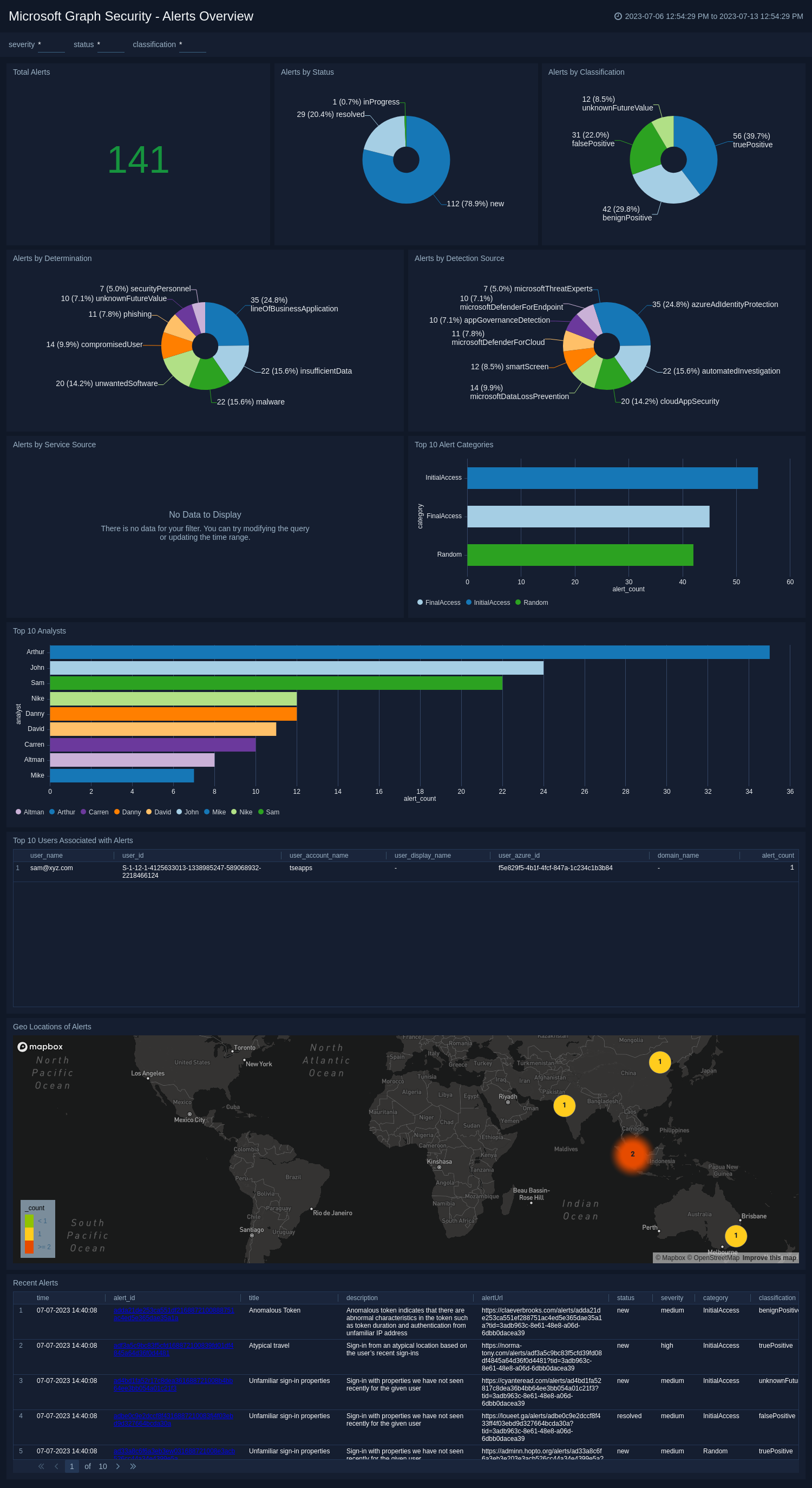
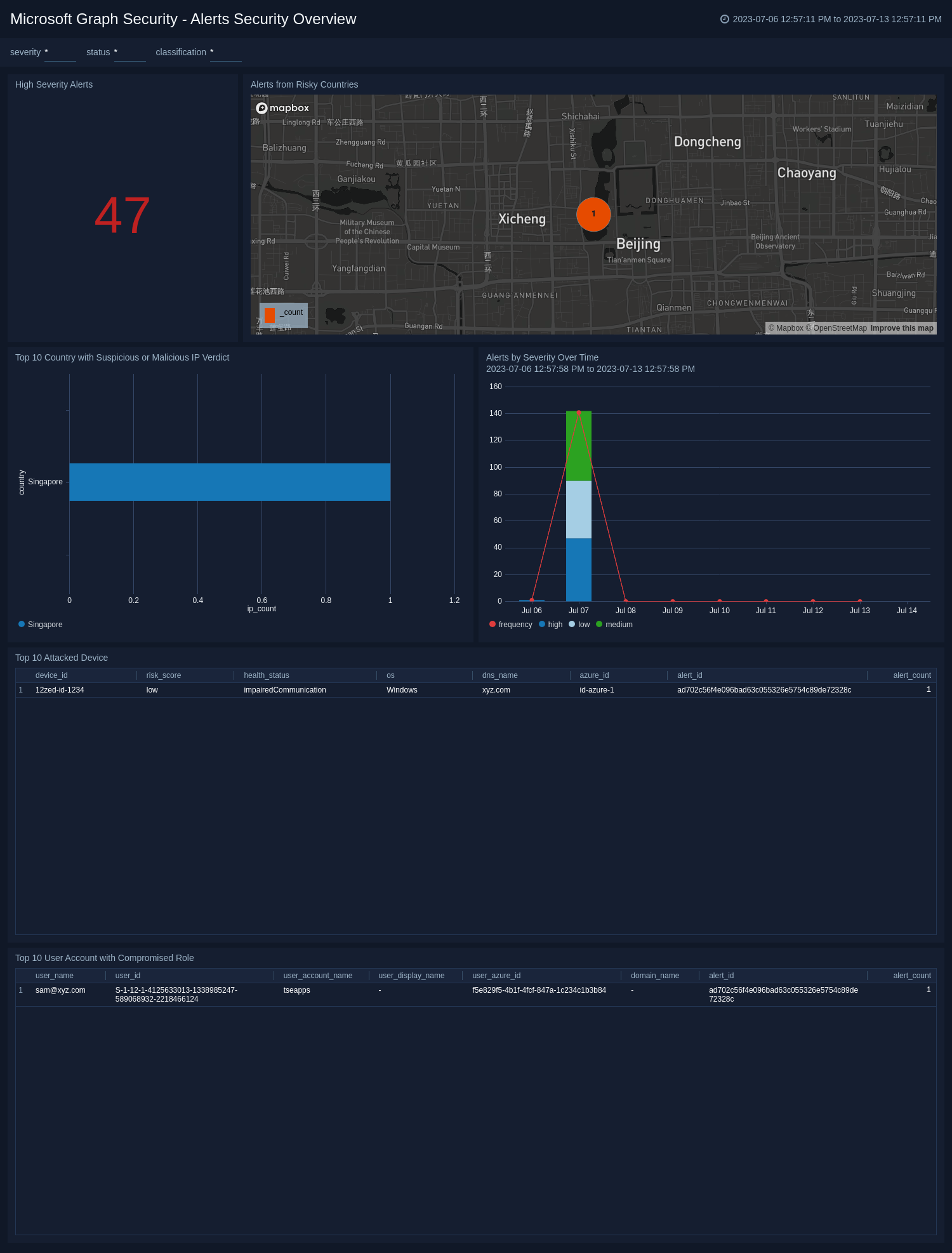
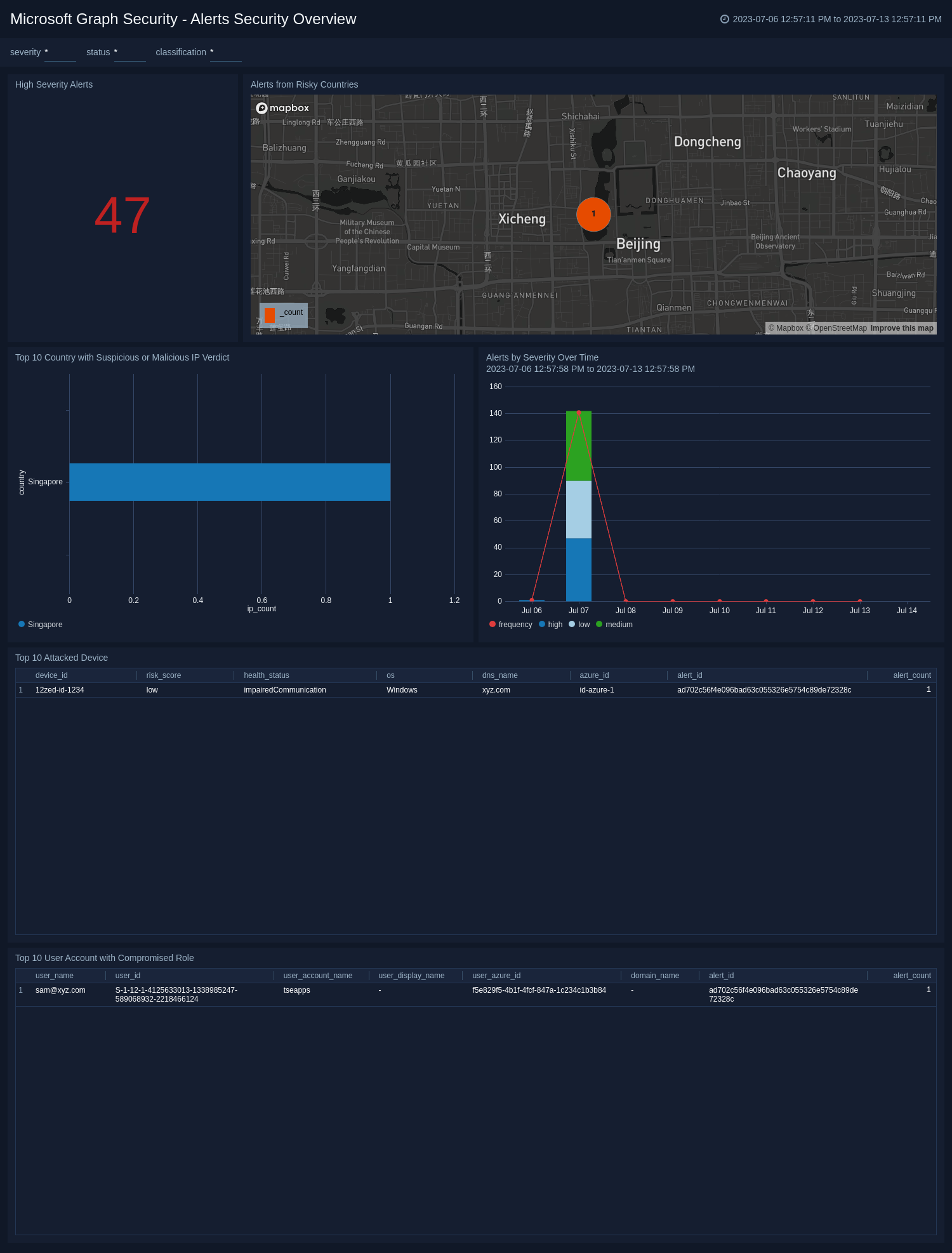
+### Alerts Security Overview
-The **Alerts Security Overview** dashboard allows you to have a high-level overview of the security posture of the organization. The dashboards include a variety of widgets including high-severity alerts. The geo-location widget highlights alerts from high-risk countries, making it easier to identify and respond to potential threats from specific locations. The severity and trend widgets provide a detailed overview of the frequency and severity of alerts over time, allowing you to take proactive measures to mitigate risks.
+The **Microsoft Graph Security - Alerts Security Overview** dashboard allows you to have a high-level overview of the security posture of the organization. The dashboards include a variety of widgets including high-severity alerts. The geo-location widget highlights alerts from high-risk countries, making it easier to identify and respond to potential threats from specific locations. The severity and trend widgets provide a detailed overview of the frequency and severity of alerts over time, allowing you to take proactive measures to mitigate risks.
The top 10 countries with malicious or suspicious IP addresses help to identify and mitigate potential threats originating from countries with a history of suspicious or malicious IP activity. The top 10 user accounts with compromised role highlights user accounts with compromised roles, necessitating immediate investigation, and remediation to protect sensitive data and system integrity. The top 10 attacked device gives an overview of the most targeted devices.
-### Microsoft Graph Security - Alerts Security Overview
+### Alerts Security Overview
-The **Alerts Security Overview** dashboard allows you to have a high-level overview of the security posture of the organization. The dashboards include a variety of widgets including high-severity alerts. The geo-location widget highlights alerts from high-risk countries, making it easier to identify and respond to potential threats from specific locations. The severity and trend widgets provide a detailed overview of the frequency and severity of alerts over time, allowing you to take proactive measures to mitigate risks.
+The **Microsoft Graph Security - Alerts Security Overview** dashboard allows you to have a high-level overview of the security posture of the organization. The dashboards include a variety of widgets including high-severity alerts. The geo-location widget highlights alerts from high-risk countries, making it easier to identify and respond to potential threats from specific locations. The severity and trend widgets provide a detailed overview of the frequency and severity of alerts over time, allowing you to take proactive measures to mitigate risks.
The top 10 countries with malicious or suspicious IP addresses help to identify and mitigate potential threats originating from countries with a history of suspicious or malicious IP activity. The top 10 user accounts with compromised role highlights user accounts with compromised roles, necessitating immediate investigation, and remediation to protect sensitive data and system integrity. The top 10 attacked device gives an overview of the most targeted devices.
 -## Uninstalling the Microsoft Graph Security app (Optional)
+## Upgrade/Downgrade the Microsoft Graph Security app (Optional)
-import AppUninstall from '../../reuse/apps/app-uninstall.md';
+import AppUpdate from '../../reuse/apps/app-update.md';
-
-## Uninstalling the Microsoft Graph Security app (Optional)
+## Upgrade/Downgrade the Microsoft Graph Security app (Optional)
-import AppUninstall from '../../reuse/apps/app-uninstall.md';
+import AppUpdate from '../../reuse/apps/app-update.md';
-}) -Akamai Security Events App allows you to visualize security events generated on the Akamai platform. The preconfigured dashboards provide insights into attack data, sources of attack, attack queries, geolocation of attack source, context on attack’s HTTP request, and rules triggered by the attack.
+Akamai Security Events app allows you to visualize security events generated on the Akamai platform. The preconfigured dashboards provide insights into attack data, sources of attack, attack queries, geolocation of attack source, context on attack’s HTTP request, and rules triggered by the attack.
## Log types
-The Akamai Security Events App uses security events generated on the Akamai platform by leveraging the [V1 SIEM API](https://developer.akamai.com/api/cloud_security/siem/v1.html) and Sumo Logic’s [Akamai SIEM API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/akamai-siem-api-source).
+The Akamai Security Events app uses security events generated on the Akamai platform by leveraging the [V1 SIEM API](https://developer.akamai.com/api/cloud_security/siem/v1.html) and Sumo Logic’s [Akamai SIEM API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/akamai-siem-api-source).
### Sample log messages
+
-Akamai Security Events App allows you to visualize security events generated on the Akamai platform. The preconfigured dashboards provide insights into attack data, sources of attack, attack queries, geolocation of attack source, context on attack’s HTTP request, and rules triggered by the attack.
+Akamai Security Events app allows you to visualize security events generated on the Akamai platform. The preconfigured dashboards provide insights into attack data, sources of attack, attack queries, geolocation of attack source, context on attack’s HTTP request, and rules triggered by the attack.
## Log types
-The Akamai Security Events App uses security events generated on the Akamai platform by leveraging the [V1 SIEM API](https://developer.akamai.com/api/cloud_security/siem/v1.html) and Sumo Logic’s [Akamai SIEM API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/akamai-siem-api-source).
+The Akamai Security Events app uses security events generated on the Akamai platform by leveraging the [V1 SIEM API](https://developer.akamai.com/api/cloud_security/siem/v1.html) and Sumo Logic’s [Akamai SIEM API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/akamai-siem-api-source).
### Sample log messages
+
@@ -75,25 +80,37 @@ _sourceCategory=
|count by attack_date, client_ip, city, country, rule_action, rule, rule_message, rule_selector, rule_version, config_id, policy_id,http_response
```
-## Collecting logs for Akamai Security Events app
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for Akamai Security Events](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/akamai-siem-api-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Akamai Security Events app is properly integrated and configured to collect and analyze your Akamai Security Events data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
-To begin collecting logs for the Sumo app for Akamai Security Events:
+}) +
+}) Duo provides two-factor authentication, endpoint remediation, and secure single sign-on tools. The Sumo Logic App for Duo Security helps you monitor your Duo account’s [authentication logs](https://duo.com/docs/adminapi#authentication-logs), [administrator logs](https://duo.com/docs/adminapi#administrator-logs), and [telephony logs](https://duo.com/docs/adminapi#telephony-logs). The dashboards provide insight into failed and successful authentications, events breakdown by applications, factors, and users, geo-location of events, admin activities, outliers, threat analysis of authentication, and administrator events.
## Log types
-The Duo Security App uses following logs. See [Duo documentation](https://duo.com/docs/adminapi#logs) for details of the log schema.
+The Duo Security App uses following logs. Refer to the [Duo documentation](https://duo.com/docs/adminapi#logs) for details of the log schema.
When you generate the Duo credentials, you should do it for the Admin API application.
-* Authentication Logs
-* Administrator Logs
-* Telephony Logs
+* Authentication logs
+* Administrator logs
+* Telephony logs
-## Collecting logs for the Duo Security app
+## Collection configuration and app installation
-To collect logs from the Duo Security App, use the new [Cloud-to-Cloud Integration for Duo Security App](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/duo-source) to create the source and use the same source category while installing the app.
+Depending on the set up collection method, you can configure and install the app in three ways:
-## Installing the Duo Security app
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
-import AppInstall2 from '../../reuse/apps/app-install-v2.md';
+:::important
+Use the [Cloud-to-Cloud Integration for Duo Security](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/duo-security-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Duo Security app is properly integrated and configured to collect and analyze your Duo Security data.
+:::
-
Duo provides two-factor authentication, endpoint remediation, and secure single sign-on tools. The Sumo Logic App for Duo Security helps you monitor your Duo account’s [authentication logs](https://duo.com/docs/adminapi#authentication-logs), [administrator logs](https://duo.com/docs/adminapi#administrator-logs), and [telephony logs](https://duo.com/docs/adminapi#telephony-logs). The dashboards provide insight into failed and successful authentications, events breakdown by applications, factors, and users, geo-location of events, admin activities, outliers, threat analysis of authentication, and administrator events.
## Log types
-The Duo Security App uses following logs. See [Duo documentation](https://duo.com/docs/adminapi#logs) for details of the log schema.
+The Duo Security App uses following logs. Refer to the [Duo documentation](https://duo.com/docs/adminapi#logs) for details of the log schema.
When you generate the Duo credentials, you should do it for the Admin API application.
-* Authentication Logs
-* Administrator Logs
-* Telephony Logs
+* Authentication logs
+* Administrator logs
+* Telephony logs
-## Collecting logs for the Duo Security app
+## Collection configuration and app installation
-To collect logs from the Duo Security App, use the new [Cloud-to-Cloud Integration for Duo Security App](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/duo-source) to create the source and use the same source category while installing the app.
+Depending on the set up collection method, you can configure and install the app in three ways:
-## Installing the Duo Security app
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
-import AppInstall2 from '../../reuse/apps/app-install-v2.md';
+:::important
+Use the [Cloud-to-Cloud Integration for Duo Security](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/duo-security-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Duo Security app is properly integrated and configured to collect and analyze your Duo Security data.
+:::
-}) -8. Go to the **Advanced** tab and click the **Enable As Web Service** checkbox under **Web Service Options**.
-9. Go to the **Share** tab, enable **Share with specific users and groups** option, add **SumoLogic_ISU** in the **Authorized Users** field, and click **OK**.
-10. Click **Done**. You can also test it by clicking the **Run** button.
-11. To get the Report URL, search for **Custom Signons and Attempted Signons Report** in the search bar and run the report.
-12. Click the **Actions** button and go to **Web Service > View URLs**.
-13. Click **OK** and copy the URL from **JSON** link. You will need this later while configuring the collection. From the URL, remove any query parameters like json, From Moment and To Moment. The report URL should look like this `https://wd2-impl-services1.workday.com/ccx/service/customreport2/
-8. Go to the **Advanced** tab and click the **Enable As Web Service** checkbox under **Web Service Options**.
-9. Go to the **Share** tab, enable **Share with specific users and groups** option, add **SumoLogic_ISU** in the **Authorized Users** field, and click **OK**.
-10. Click **Done**. You can also test it by clicking the **Run** button.
-11. To get the Report URL, search for **Custom Signons and Attempted Signons Report** in the search bar and run the report.
-12. Click the **Actions** button and go to **Web Service > View URLs**.
-13. Click **OK** and copy the URL from **JSON** link. You will need this later while configuring the collection. From the URL, remove any query parameters like json, From Moment and To Moment. The report URL should look like this `https://wd2-impl-services1.workday.com/ccx/service/customreport2///`.
-
-### Step 2: Add a Hosted Collector and HTTP Source
-
-:::note
-This step is not needed if you're configuring the [Cloud-to-Cloud Collector Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/workday-source/).
-:::
+## Collection configuration and app installation
+
+import CollectionConfiguration from '../../reuse/apps/collection-configuration.md';
-In this step, you create a hosted collector and HTTP source to receive data from the scripts that collect data from your Workday tenant.
+
## Collection configuration and app installation
-Depending on the set up collection method, you can configure and install the app in three ways:
+import CollectionConfiguration from '../../reuse/apps/collection-configuration.md';
-- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
-- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
-- **[Use existing source and install the app](#use-an-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+}) +8. Go to the **Advanced** tab and click the **Enable As Web Service** checkbox under **Web Service Options**.
+9. Go to the **Share** tab, enable **Share with specific users and groups** option, add **SumoLogic_ISU** in the **Authorized Users** field, and click **OK**.
+10. Click **Done**. You can also test it by clicking the **Run** button.
+11. To get the Report URL, search for **Custom Signons and Attempted Signons Report** in the search bar and run the report.
+12. Click the **Actions** button and go to **Web Service > View URLs**.
+13. Click **OK** and copy the URL from **JSON** link. You will need this later while configuring the collection. From the URL, remove any query parameters like json, From Moment and To Moment. The report URL should look like this `https://wd2-impl-services1.workday.com/ccx/service/customreport2/
+8. Go to the **Advanced** tab and click the **Enable As Web Service** checkbox under **Web Service Options**.
+9. Go to the **Share** tab, enable **Share with specific users and groups** option, add **SumoLogic_ISU** in the **Authorized Users** field, and click **OK**.
+10. Click **Done**. You can also test it by clicking the **Run** button.
+11. To get the Report URL, search for **Custom Signons and Attempted Signons Report** in the search bar and run the report.
+12. Click the **Actions** button and go to **Web Service > View URLs**.
+13. Click **OK** and copy the URL from **JSON** link. You will need this later while configuring the collection. From the URL, remove any query parameters like json, From Moment and To Moment. The report URL should look like this `https://wd2-impl-services1.workday.com/ccx/service/customreport2///`.
### Source configuration
@@ -50,14 +141,14 @@ To configure a Workday Source, follow the steps below:
7. **Fields** (Optional). Click the **+Add** field link to define the fields you want to associate. Each field needs a name (key) and value.
*  A green circle with a checkmark is shown when the field exists in the Fields table schema.
*  An orange triangle with an exclamation point is shown when the field doesn't exist in the Fields table schema. In this case, an option to automatically add the nonexistent fields to the Fields table schema is provided. If a field is sent to Sumo that does not exist in the Fields schema it is ignored, known as dropped.
-8. **SignOn Report URL**. Paste the SignOn Report URL from [Step 1.5](/docs/integrations/saas-cloud/workday.md#step-15-create-a-custom-sign-on-report).
-9. **Integration System User Name**. Name of the account (SumoLogic_ISU) created in [Step 1.1](/docs/integrations/saas-cloud/workday.md#step-11-create-an-integration-system-user).
-10. **Integration System User Password**. The password of the account created in [Step 1.1](/docs/integrations/saas-cloud/workday.md#step-11-create-an-integration-system-user).
-11. **Refresh Token URL**. Paste the Token endpoint copied from [Step 1.3](/docs/integrations/saas-cloud/workday/#step-13-register-the-api-client).
-12. **Client ID**. Paste the Client ID copied from [Step 1.3](/docs/integrations/saas-cloud/workday/#step-13-register-the-api-client).
-13. **Client Secret**. Paste the Client Secret copied from [Step 1.3](/docs/integrations/saas-cloud/workday/#step-13-register-the-api-client).
-14. **Refresh Token**. Paste the generated Refresh Token copied from [Step 1.3](/docs/integrations/saas-cloud/workday/#step-13-register-the-api-client).
-15. **REST API URL**. Take the Workday Rest API endpoint copied in [Step 1.3](/docs/integrations/saas-cloud/workday/#step-13-register-the-api-client) and modify it to match the format `https:///ccx/api/privacy/v1//activityLogging`. Provide the modified URL here.
+8. **SignOn Report URL**. Paste the SignOn Report URL from the [Vendor configuration: Step 5](#step-5-create-a-custom-sign-on-report).
+9. **Integration System User Name**. Name of the account (SumoLogic_ISU) created in [Vendor configuration: Step 1](#step-1-create-an-integration-system-user).
+10. **Integration System User Password**. The password of the account created in [Vendor configuration: Step 1](#step-1-create-an-integration-system-user).
+11. **Refresh Token URL**. Paste the Token endpoint copied from [Vendor configuration: Step 3](#step-3-register-the-api-client).
+12. **Client ID**. Paste the Client ID copied from [Vendor configuration: Step 3](#step-3-register-the-api-client).
+13. **Client Secret**. Paste the Client Secret copied from [Vendor configuration: Step 3](#step-3-register-the-api-client).
+14. **Refresh Token**. Paste the generated Refresh Token copied from [Vendor configuration: Step3](#step-3-register-the-api-client).
+15. **REST API URL**. Take the Workday Rest API endpoint copied in [Vendor configuration: Step 3](#step-3-register-the-api-client) and modify it to match the format `https:///ccx/api/privacy/v1//activityLogging`. Provide the modified URL here.
16. **Collection Should begin** (Optional). Select the time range for how far back you want this source to start collecting data from Workday. This is set to **24 Hours ago** by default.
:::note
Sample Alert Log (click to expand)
+Sample Alert Log
-```json title="Sample Alert Log" +```json { "id":"adf3a5c9bc83f5cfd39fd01df4845a64d36f0d4481", "providerAlertId":"5bd1db63c29f8f4f17e6be7f8b4b5470199759916a3adee797b414fbaf6b1af1", @@ -183,48 +183,66 @@ _sourceCategory="ms_alerts" | count_distinct(alert_id) ``` -## Set up collection +## Collection configuration and app installation -Follow the instructions for setting up [Cloud-to-Cloud Integration for Microsoft Graph Security](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-security-api-source/) app to create the source and use the same source category while installing the app. +Depending on the set up collection method, you can configure and install the app in three ways: -## Installing the Microsoft Graph Security app +- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or +- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or +- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app. -This section has instructions for installing the Microsoft Graph Security app for Sumo Logic and a description of the dashboard. Configure Microsoft Graph Security app using the steps described in the [Microsoft Graph Security Cloud-to-Cloud Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-security-api-source/). +:::important +Use the [Cloud-to-Cloud Integration for Microsoft Graph Security](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/microsoft-graph-security-api-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Microsoft Graph Security app is properly integrated and configured to collect and analyze your Microsoft Graph Security data. +::: -import AppInstall2 from '../../reuse/apps/app-install-v2.md'; +### Create a new collector and install the app -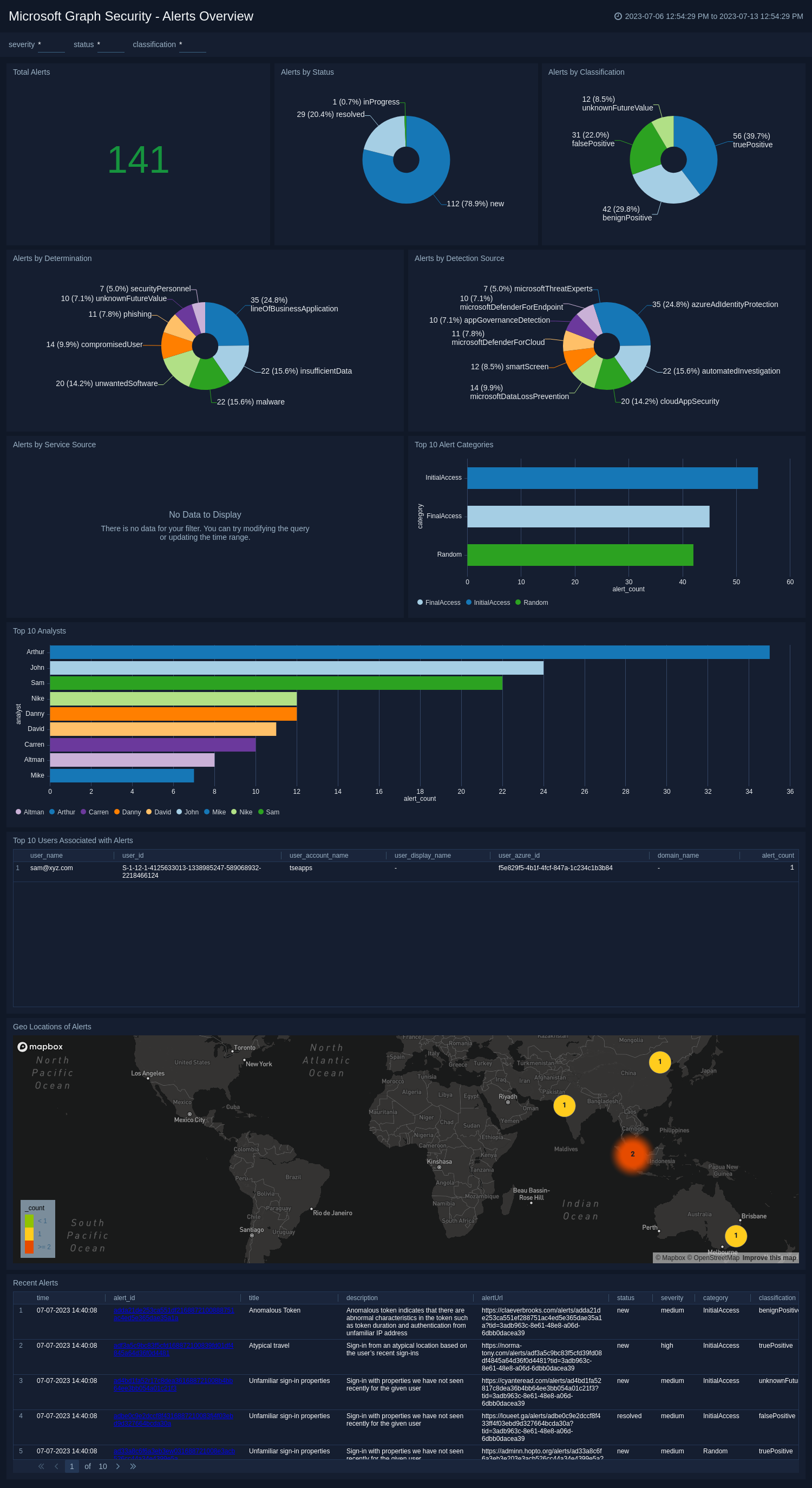 -### Microsoft Graph Security - Alerts Security Overview
+### Alerts Security Overview
-The **Alerts Security Overview** dashboard allows you to have a high-level overview of the security posture of the organization. The dashboards include a variety of widgets including high-severity alerts. The geo-location widget highlights alerts from high-risk countries, making it easier to identify and respond to potential threats from specific locations. The severity and trend widgets provide a detailed overview of the frequency and severity of alerts over time, allowing you to take proactive measures to mitigate risks.
+The **Microsoft Graph Security - Alerts Security Overview** dashboard allows you to have a high-level overview of the security posture of the organization. The dashboards include a variety of widgets including high-severity alerts. The geo-location widget highlights alerts from high-risk countries, making it easier to identify and respond to potential threats from specific locations. The severity and trend widgets provide a detailed overview of the frequency and severity of alerts over time, allowing you to take proactive measures to mitigate risks.
The top 10 countries with malicious or suspicious IP addresses help to identify and mitigate potential threats originating from countries with a history of suspicious or malicious IP activity. The top 10 user accounts with compromised role highlights user accounts with compromised roles, necessitating immediate investigation, and remediation to protect sensitive data and system integrity. The top 10 attacked device gives an overview of the most targeted devices.
-### Microsoft Graph Security - Alerts Security Overview
+### Alerts Security Overview
-The **Alerts Security Overview** dashboard allows you to have a high-level overview of the security posture of the organization. The dashboards include a variety of widgets including high-severity alerts. The geo-location widget highlights alerts from high-risk countries, making it easier to identify and respond to potential threats from specific locations. The severity and trend widgets provide a detailed overview of the frequency and severity of alerts over time, allowing you to take proactive measures to mitigate risks.
+The **Microsoft Graph Security - Alerts Security Overview** dashboard allows you to have a high-level overview of the security posture of the organization. The dashboards include a variety of widgets including high-severity alerts. The geo-location widget highlights alerts from high-risk countries, making it easier to identify and respond to potential threats from specific locations. The severity and trend widgets provide a detailed overview of the frequency and severity of alerts over time, allowing you to take proactive measures to mitigate risks.
The top 10 countries with malicious or suspicious IP addresses help to identify and mitigate potential threats originating from countries with a history of suspicious or malicious IP activity. The top 10 user accounts with compromised role highlights user accounts with compromised roles, necessitating immediate investigation, and remediation to protect sensitive data and system integrity. The top 10 attacked device gives an overview of the most targeted devices.
 -## Uninstalling the Microsoft Graph Security app (Optional)
+## Upgrade/Downgrade the Microsoft Graph Security app (Optional)
-import AppUninstall from '../../reuse/apps/app-uninstall.md';
+import AppUpdate from '../../reuse/apps/app-update.md';
-
-## Uninstalling the Microsoft Graph Security app (Optional)
+## Upgrade/Downgrade the Microsoft Graph Security app (Optional)
-import AppUninstall from '../../reuse/apps/app-uninstall.md';
+import AppUpdate from '../../reuse/apps/app-update.md';
-
+
+
## Sample queries
```sql title="Unique Inbound Domains"
@@ -146,15 +151,35 @@ _sourceCategory="pod_src"
| count_distinct(inbound_domain)
```
-## Set up collection
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for Proofpoint on Demand](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/proofpoint-on-demand-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Proofpoint on Demand app is properly integrated and configured to collect and analyze your Proofpoint on Demand data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+Message log
+ +```json { "final_module": "access", "msg": { @@ -129,6 +132,8 @@ This app uses Proofpoint on Demand source to collect the data from Proofpoint on } } ``` +
+
+
+Sample Message Event
+ +```json { "GUID": "qop94nlsUdvm1BsHU_8jdPXWYH0ZCndT", "QID": "3qk94m8jy1-1", @@ -105,7 +108,12 @@ This app uses [Proofpoint TAP source](/docs/send-data/hosted-collectors/cloud-to "xmailer": null } ``` -```json title="Sample Clicks Log" +
+
## Sample queries
@@ -155,15 +164,35 @@ _sourceCategory="milan_proofpoint_tap" ("CLICK_PERMITTED" or "CLICK_BLOCKED")
| count_distinct(id)
```
-## Set up collection
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for Proofpoint TAP](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/proofpoint-tap-source/) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Proofpoint TAP app is properly integrated and configured to collect and analyze your Proofpoint TAP data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+Sample Clicks Log
+ +```json { "GUID": "6Qpm37_BE3mFckkZEAZtUSrA8t9FyQSm", "campaignID": "3qsaakgeb2-1", @@ -126,6 +134,7 @@ This app uses [Proofpoint TAP source](/docs/send-data/hosted-collectors/cloud-to "threatUrl": "https://threatinsight.proofpoint.com/e659ac2e/threat/email/bb56ef875eca495366175" } ``` +
+
+
+Asset Log
+ +```json { "assessed_for_policies": false, "assessed_for_vulnerabilities": true, @@ -89,7 +92,12 @@ This app uses Sumo Logic’s Rapid7 Source to collect [assets](https://help.rapi "unique_identifiers": [] } ``` -```json title="Vulnerability Finding Log" +
+
+
+Vulnerability Finding Log
+ +```json { "asset_id": "4b8cdd43-3bd3-411a-9597-41aedf04b62f-default-asset-519", "check_id": null, @@ -108,8 +116,12 @@ This app uses Sumo Logic’s Rapid7 Source to collect [assets](https://help.rapi "vulnerability_id": "generic-tcp-timestamp" } ``` +
+
+
## Sample queries
```sql title="Assets by Type"
@@ -203,15 +217,35 @@ on vulnerability.id=asset_vulnerability.vulnerability_id // get information of a
| limit 10
```
-## Set up collection
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for Rapid7](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/rapid7-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Rapid7 app is properly integrated and configured to collect and analyze your Rapid7 data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+Vulnerability Log
-```json title="Vulnerability Log" +```json { "added": "2018-02-06T00:00:00Z", "categories": "XSS,jQuery", @@ -177,6 +189,8 @@ This app uses Sumo Logic’s Rapid7 Source to collect [assets](https://help.rapi "title": "jQuery Vulnerability: CVE-2015-9251" } ``` +
+
+
+Sample Threats Log Messages
+ +```json { "agentDetectionInfo": { "accountId": "11384404", @@ -203,8 +206,12 @@ The Sumo Logic app for SentinelOne consumes Threats and Agents logs, refer to th ] } ``` +
+
## Sample queries
@@ -336,11 +343,35 @@ _sourceCategory=sentinelone uuid
| count_distinct (id)
```
-## Installing the SentinelOne app
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for SentinelOne](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/sentinelone-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your SentinelOne app is properly integrated and configured to collect and analyze your SentinelOne data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+Sample Agents Log Messages
-```json title="Sample Agents Log Messages" +```json { "accountId": "113841926404", "accountName": "Health Lobby", @@ -310,7 +317,7 @@ The Sumo Logic app for SentinelOne consumes Threats and Agents logs, refer to th "uuid": "be20d732fc87bd479e0a" } ``` - +
+
+
+User logs
+ ```json { "id": "UM27LNGHK", @@ -61,8 +63,11 @@ The following table provides sample log messages for the different log types. "logType": "UserLog" } ``` +
+
+
+Public Channel logs
-[Public Channel logs](https://api.slack.com/methods/conversations.list) ```json { "channel_id": "CKN1D8010", @@ -72,8 +77,11 @@ The following table provides sample log messages for the different log types. "teamName": "TestSlack" } ``` +
+
+
+Public Message logs
-[Public Message logs](https://api.slack.com/methods) ```json { "type": "message", @@ -110,8 +118,11 @@ The following table provides sample log messages for the different log types. "logType": "ConversationLog" } ``` +
+
+
+Access logs
-[Access logs](https://api.slack.com/methods/team.accessLogs) ```json { "user_id": "e65b0476", @@ -128,8 +139,11 @@ The following table provides sample log messages for the different log types. "logType": "AccessLog" } ``` +
+
### Sample queries
@@ -215,15 +230,35 @@ _sourceCategory=Labs/slack
| limit 20
```
-## Collect logs for the Slack app
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for Slack](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/slack-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Slack app is properly integrated and configured to collect and analyze your Slack data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+Audit logs
-[Audit logs](https://api.slack.com/docs/audit-logs-api#the_audit_event) ```json { "logType": "UserAuditLog", @@ -187,6 +201,7 @@ The following table provides sample log messages for the different log types. } } ``` +}) -Akamai Security Events App allows you to visualize security events generated on the Akamai platform. The preconfigured dashboards provide insights into attack data, sources of attack, attack queries, geolocation of attack source, context on attack’s HTTP request, and rules triggered by the attack.
+Akamai Security Events app allows you to visualize security events generated on the Akamai platform. The preconfigured dashboards provide insights into attack data, sources of attack, attack queries, geolocation of attack source, context on attack’s HTTP request, and rules triggered by the attack.
## Log types
-The Akamai Security Events App uses security events generated on the Akamai platform by leveraging the [V1 SIEM API](https://developer.akamai.com/api/cloud_security/siem/v1.html) and Sumo Logic’s [Akamai SIEM API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/akamai-siem-api-source).
+The Akamai Security Events app uses security events generated on the Akamai platform by leveraging the [V1 SIEM API](https://developer.akamai.com/api/cloud_security/siem/v1.html) and Sumo Logic’s [Akamai SIEM API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/akamai-siem-api-source).
### Sample log messages
+
-Akamai Security Events App allows you to visualize security events generated on the Akamai platform. The preconfigured dashboards provide insights into attack data, sources of attack, attack queries, geolocation of attack source, context on attack’s HTTP request, and rules triggered by the attack.
+Akamai Security Events app allows you to visualize security events generated on the Akamai platform. The preconfigured dashboards provide insights into attack data, sources of attack, attack queries, geolocation of attack source, context on attack’s HTTP request, and rules triggered by the attack.
## Log types
-The Akamai Security Events App uses security events generated on the Akamai platform by leveraging the [V1 SIEM API](https://developer.akamai.com/api/cloud_security/siem/v1.html) and Sumo Logic’s [Akamai SIEM API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/akamai-siem-api-source).
+The Akamai Security Events app uses security events generated on the Akamai platform by leveraging the [V1 SIEM API](https://developer.akamai.com/api/cloud_security/siem/v1.html) and Sumo Logic’s [Akamai SIEM API Source](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/akamai-siem-api-source).
### Sample log messages
+
+
+
-## Sample queries
+### Sample queries
```sql
_sourceCategory=Click to view the log message
+ ```json { "type": "akamai_siem", @@ -63,8 +67,9 @@ The Akamai Security Events App uses security events generated on the Akamai plat } } ``` +
+
+
+Detection Event
+ +```json +{ "metadata": { "customerIDString": “xxxxxxxxxxxxxxxxxxxxxxxxxxxxxx", "offset": 14947764, @@ -84,7 +86,12 @@ For more information on Events, please refer to [Streaming API Event Dictionary] } ``` -```json title="Authentication Event" +
+
+
+Authentication Event
+ +```json { "event": { "AuditKeyValues": [ @@ -109,6 +116,11 @@ For more information on Events, please refer to [Streaming API Event Dictionary] }NOPQRSTUV","eventType":"AuthActivityAuditEvent","eventCreationTime":1480375833,"offset":80960}} ``` +
+
### Sample queries
@@ -181,16 +194,35 @@ _sourceCategory=*Crowdstrike* UserActivityAuditEvent
| sort by _count
```
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for CrowdStrike](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/crowdstrike-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your CrowdStrike app is properly integrated and configured to collect and analyze your CrowdStrike data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+Detection Status Update
+ ```json title="Detection Status Update" { "metadata": { @@ -144,6 +156,7 @@ For more information on Events, please refer to [Streaming API Event Dictionary] } } ``` +}) +
+}) Duo provides two-factor authentication, endpoint remediation, and secure single sign-on tools. The Sumo Logic App for Duo Security helps you monitor your Duo account’s [authentication logs](https://duo.com/docs/adminapi#authentication-logs), [administrator logs](https://duo.com/docs/adminapi#administrator-logs), and [telephony logs](https://duo.com/docs/adminapi#telephony-logs). The dashboards provide insight into failed and successful authentications, events breakdown by applications, factors, and users, geo-location of events, admin activities, outliers, threat analysis of authentication, and administrator events.
## Log types
-The Duo Security App uses following logs. See [Duo documentation](https://duo.com/docs/adminapi#logs) for details of the log schema.
+The Duo Security App uses following logs. Refer to the [Duo documentation](https://duo.com/docs/adminapi#logs) for details of the log schema.
When you generate the Duo credentials, you should do it for the Admin API application.
-* Authentication Logs
-* Administrator Logs
-* Telephony Logs
+* Authentication logs
+* Administrator logs
+* Telephony logs
-## Collecting logs for the Duo Security app
+## Collection configuration and app installation
-To collect logs from the Duo Security App, use the new [Cloud-to-Cloud Integration for Duo Security App](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/duo-source) to create the source and use the same source category while installing the app.
+Depending on the set up collection method, you can configure and install the app in three ways:
-## Installing the Duo Security app
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
-import AppInstall2 from '../../reuse/apps/app-install-v2.md';
+:::important
+Use the [Cloud-to-Cloud Integration for Duo Security](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/duo-security-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Duo Security app is properly integrated and configured to collect and analyze your Duo Security data.
+:::
-
Duo provides two-factor authentication, endpoint remediation, and secure single sign-on tools. The Sumo Logic App for Duo Security helps you monitor your Duo account’s [authentication logs](https://duo.com/docs/adminapi#authentication-logs), [administrator logs](https://duo.com/docs/adminapi#administrator-logs), and [telephony logs](https://duo.com/docs/adminapi#telephony-logs). The dashboards provide insight into failed and successful authentications, events breakdown by applications, factors, and users, geo-location of events, admin activities, outliers, threat analysis of authentication, and administrator events.
## Log types
-The Duo Security App uses following logs. See [Duo documentation](https://duo.com/docs/adminapi#logs) for details of the log schema.
+The Duo Security App uses following logs. Refer to the [Duo documentation](https://duo.com/docs/adminapi#logs) for details of the log schema.
When you generate the Duo credentials, you should do it for the Admin API application.
-* Authentication Logs
-* Administrator Logs
-* Telephony Logs
+* Authentication logs
+* Administrator logs
+* Telephony logs
-## Collecting logs for the Duo Security app
+## Collection configuration and app installation
-To collect logs from the Duo Security App, use the new [Cloud-to-Cloud Integration for Duo Security App](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/duo-source) to create the source and use the same source category while installing the app.
+Depending on the set up collection method, you can configure and install the app in three ways:
-## Installing the Duo Security app
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
-import AppInstall2 from '../../reuse/apps/app-install-v2.md';
+:::important
+Use the [Cloud-to-Cloud Integration for Duo Security](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/duo-security-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Duo Security app is properly integrated and configured to collect and analyze your Duo Security data.
+:::
-
@@ -76,9 +72,8 @@ To collect logs from the Netskope platform, use the [new Cloud-to-Cloud Integrat
"os": "Windows 8",
"browser": "Internet Explorer",
"appcategory": "Webmail"
- }
- ]
}
+
```
@@ -99,18 +94,37 @@ to_user, app_session_id nodrop
| count
```
-## Installing the Netskope app
+## Collection configuration and app installation
+
+Depending on the set up collection method, you can configure and install the app in three ways:
+
+- **[Create a new collector and install the app](#create-a-new-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under a new Sumo Logic Collector and later install the app; Or
+- **[Use an existing collector and install the app](#use-an-existing-collector-and-install-the-app)**. Create a new Sumo Logic Cloud-to-Cloud (C2C) source under an existing Sumo Logic Collector and later install the app; Or
+- **[Use existing source and install the app](#use-existing-source-and-install-the-app)**. Use your existing configured Sumo Logic Cloud-to-Cloud (C2C) source and install the app.
+
+:::important
+Use the [Cloud-to-Cloud Integration for Netskope](/docs/send-data/hosted-collectors/cloud-to-cloud-integration-framework/netskope-source) to create the source and use the same source category while installing the app. By following these steps, you can ensure that your Netskope app is properly integrated and configured to collect and analyze your Netskope data.
+:::
+
+### Create a new collector and install the app
+
+import AppCollectionOPtion1 from '../../reuse/apps/app-collection-option-1.md';
+
+}) -8. Go to the **Advanced** tab and click the **Enable As Web Service** checkbox under **Web Service Options**.
-9. Go to the **Share** tab, enable **Share with specific users and groups** option, add **SumoLogic_ISU** in the **Authorized Users** field, and click **OK**.
-10. Click **Done**. You can also test it by clicking the **Run** button.
-11. To get the Report URL, search for **Custom Signons and Attempted Signons Report** in the search bar and run the report.
-12. Click the **Actions** button and go to **Web Service > View URLs**.
-13. Click **OK** and copy the URL from **JSON** link. You will need this later while configuring the collection. From the URL, remove any query parameters like json, From Moment and To Moment. The report URL should look like this `https://wd2-impl-services1.workday.com/ccx/service/customreport2/
-8. Go to the **Advanced** tab and click the **Enable As Web Service** checkbox under **Web Service Options**.
-9. Go to the **Share** tab, enable **Share with specific users and groups** option, add **SumoLogic_ISU** in the **Authorized Users** field, and click **OK**.
-10. Click **Done**. You can also test it by clicking the **Run** button.
-11. To get the Report URL, search for **Custom Signons and Attempted Signons Report** in the search bar and run the report.
-12. Click the **Actions** button and go to **Web Service > View URLs**.
-13. Click **OK** and copy the URL from **JSON** link. You will need this later while configuring the collection. From the URL, remove any query parameters like json, From Moment and To Moment. The report URL should look like this `https://wd2-impl-services1.workday.com/ccx/service/customreport2/}) +8. Go to the **Advanced** tab and click the **Enable As Web Service** checkbox under **Web Service Options**.
+9. Go to the **Share** tab, enable **Share with specific users and groups** option, add **SumoLogic_ISU** in the **Authorized Users** field, and click **OK**.
+10. Click **Done**. You can also test it by clicking the **Run** button.
+11. To get the Report URL, search for **Custom Signons and Attempted Signons Report** in the search bar and run the report.
+12. Click the **Actions** button and go to **Web Service > View URLs**.
+13. Click **OK** and copy the URL from **JSON** link. You will need this later while configuring the collection. From the URL, remove any query parameters like json, From Moment and To Moment. The report URL should look like this `https://wd2-impl-services1.workday.com/ccx/service/customreport2/
+8. Go to the **Advanced** tab and click the **Enable As Web Service** checkbox under **Web Service Options**.
+9. Go to the **Share** tab, enable **Share with specific users and groups** option, add **SumoLogic_ISU** in the **Authorized Users** field, and click **OK**.
+10. Click **Done**. You can also test it by clicking the **Run** button.
+11. To get the Report URL, search for **Custom Signons and Attempted Signons Report** in the search bar and run the report.
+12. Click the **Actions** button and go to **Web Service > View URLs**.
+13. Click **OK** and copy the URL from **JSON** link. You will need this later while configuring the collection. From the URL, remove any query parameters like json, From Moment and To Moment. The report URL should look like this `https://wd2-impl-services1.workday.com/ccx/service/customreport2/}) +
+}) +The **Airtable - Overview** dashboard provides a high-level view of key metrics related to Airtable platform user activity, audits, and execution. It contains widgets that display data such as total audit logs and failed executions, action distribution, and top-performing actions and users. The dashboard also provides information on activity trends over time and user locations. The Audit Log Summary widget provides a quick overview of all platform activity. Overall, the dashboard helps users quickly understand how the platform is used and identify areas for improvement.
+The **Airtable - Overview** dashboard provides a high-level view of key metrics related to Airtable platform user activity, audits, and execution. It contains widgets that display data such as total audit logs and failed executions, action distribution, and top-performing actions and users. The dashboard also provides information on activity trends over time and user locations. The Audit Log Summary widget provides a quick overview of all platform activity. Overall, the dashboard helps users quickly understand how the platform is used and identify areas for improvement.}) +
+})
})
}) -1. Authorize your app by following the steps in [Authorize](https://developer.box.com/guides/authentication/jwt/jwt-setup/#app-authorization).
-
-
-### States
-
-A Box Source tracks errors, reports its health, and start-up progress. You’re informed, in real-time, if the Source is having trouble connecting, if there's an error requiring user action, or if it is healthy and collecting by utilizing [Health Events](/docs/manage/health-events).
-
-A Box Source goes through the following states when created:
-1. **Pending**. Once the Source is submitted, it is validated, stored, and placed in a **Pending** state.
-1. **Started**. A collection task is created on the Hosted Collector.
-1. **Initialized**. The task configuration is complete in Sumo Logic.
-1. **Authenticated**. The Source successfully authenticated with Box.
-1. **Collecting**. The Source is actively collecting data from Box.
-
-If the Source has any issues during any one of these states, it is placed in an **Error** state.
-
-When you delete the Source, it is placed in a **Stopping** state. When it has successfully stopped, it is deleted from your Hosted Collector.
-
-On the Collection page, the [Health](/docs/manage/health-events#collection-page) and Status for Sources is displayed. Use [Health Events](/docs/manage/health-events) to investigate issues with collection.
-1. Authorize your app by following the steps in [Authorize](https://developer.box.com/guides/authentication/jwt/jwt-setup/#app-authorization).
-
-
-### States
-
-A Box Source tracks errors, reports its health, and start-up progress. You’re informed, in real-time, if the Source is having trouble connecting, if there's an error requiring user action, or if it is healthy and collecting by utilizing [Health Events](/docs/manage/health-events).
-
-A Box Source goes through the following states when created:
-1. **Pending**. Once the Source is submitted, it is validated, stored, and placed in a **Pending** state.
-1. **Started**. A collection task is created on the Hosted Collector.
-1. **Initialized**. The task configuration is complete in Sumo Logic.
-1. **Authenticated**. The Source successfully authenticated with Box.
-1. **Collecting**. The Source is actively collecting data from Box.
-
-If the Source has any issues during any one of these states, it is placed in an **Error** state.
-
-When you delete the Source, it is placed in a **Stopping** state. When it has successfully stopped, it is deleted from your Hosted Collector.
-
-On the Collection page, the [Health](/docs/manage/health-events#collection-page) and Status for Sources is displayed. Use [Health Events](/docs/manage/health-events) to investigate issues with collection.}) -
-You can click the text in the Health column, such as **Error**, to open the issue in Health Events to investigate.
-
-You can click the text in the Health column, such as **Error**, to open the issue in Health Events to investigate.}) -
-Hover your mouse over the status icon to view a tooltip with details on the detected issue.
-
-Hover your mouse over the status icon to view a tooltip with details on the detected issue.}) -
-### Create a Box source
-
-When you create a Box Source, you add it to a Hosted Collector. Before creating the Source, identify the Hosted Collector you want to use or create a new Hosted Collector. For instructions, see [Create a Hosted Collector](/docs/send-data/hosted-collectors/configure-hosted-collector).
-
-To configure a Box Source:
-1. [**Classic UI**](/docs/get-started/sumo-logic-ui-classic). In the main Sumo Logic menu, select **Manage Data > Collection > Collection**.
-
-### Create a Box source
-
-When you create a Box Source, you add it to a Hosted Collector. Before creating the Source, identify the Hosted Collector you want to use or create a new Hosted Collector. For instructions, see [Create a Hosted Collector](/docs/send-data/hosted-collectors/configure-hosted-collector).
-
-To configure a Box Source:
-1. [**Classic UI**](/docs/get-started/sumo-logic-ui-classic). In the main Sumo Logic menu, select **Manage Data > Collection > Collection**. }) -1. Enter a **Name** for the Source. The **description** is optional.
-1. Enter a **Name** for the Source. The **description** is optional. }) -1. (Optional) For **Source Category**, enter any string to tag the output collected from the Source. Category [metadata](/docs/search/get-started-with-search/search-basics/built-in-metadata) is stored in a searchable field called `_sourceCategory`.
-1. **Forward to SIEM**. Check the checkbox to forward your data to [Cloud SIEM](/docs/cse).
-1. (Optional) For **Source Category**, enter any string to tag the output collected from the Source. Category [metadata](/docs/search/get-started-with-search/search-basics/built-in-metadata) is stored in a searchable field called `_sourceCategory`.
-1. **Forward to SIEM**. Check the checkbox to forward your data to [Cloud SIEM](/docs/cse).