-
Notifications
You must be signed in to change notification settings - Fork 17
Description
Please do not report security vulnerabilities here. The Responsible Disclosure Program details the procedure for disclosing security issues.
Thank you in advance for helping us to improve this library! Please read through the template below and answer all relevant questions. Your additional work here is greatly appreciated and will help us respond as quickly as possible. For general support or usage questions, use the Auth0 Community or Auth0 Support. Finally, to avoid duplicates, please search existing Issues before submitting one here.
By submitting an Issue to this repository, you agree to the terms within the Auth0 Code of Conduct.
Description
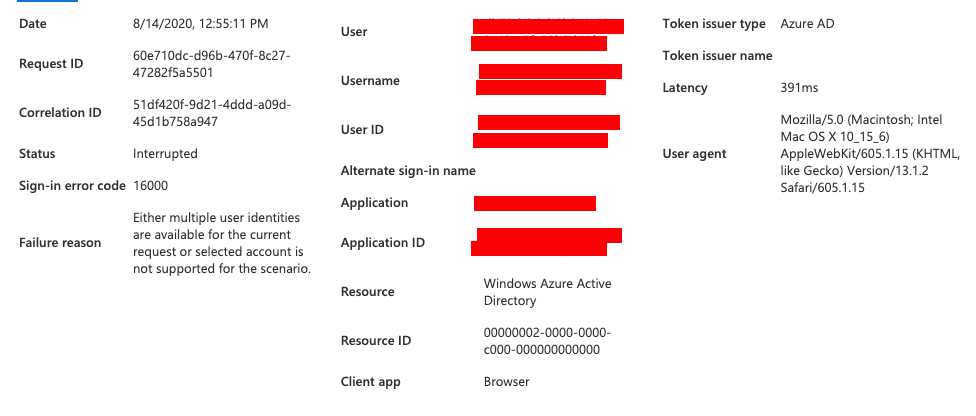
After being redirected to the azure ad login screen I'm redirected back to the failureRedirect. In the Activity > "Sign-ins" view in enterprise applications I get two events for every login attempt. One "Success" and one "Interrupted."
The interrupted one has error code 16000 with failure reason "Either multiple user identities are available for the current request or selected account is not supported for the scenario."
Reproduction
- Code sample
import { Router } from 'express';
import cors from 'cors';
import AuthController from 'controllers/admin-controllers/accessManagement/AuthController';
import UserController from 'controllers/admin-controllers/organization/UserController';
import passport from 'passport';
import * as jwt from 'jsonwebtoken';
import issueJWT from 'utils/IssueToken';
import { IGetUserAuthInfoRequest } from 'typeDefs/definitionsfile';
import { Utils } from 'utils/classes/Utils';
const AzureAdOAuth2Strategy = require('passport-azure-ad-oauth2').Strategy;
export class UserRouter {
public router: Router;
private azureAdOauth2 = new AzureAdOAuth2Strategy(
{
clientID: process.env.AZURE_OAUTH_CLIENT_ID,
clientSecret: process.env.AZURE_OAUTH_CLIENT_SECRET,
callbackURL: '/auth/login/azure/return',
tenant: process.env.AZURE_OAUTH_TENANT,
},
async (accessToken, refreshToken, params, profile, done) => {
const decodedToken = jwt.decode(accessToken);
await Utils.checkLogin({ email: decodedToken.email, password: null, localUser: false, isInternal: true })
.then(user => {
const permissions = Utils.populatePermission(user);
const token = issueJWT(user);
const accessObject = {
token,
user,
permissions,
};
return done(null, accessObject);
})
.catch(error => {
return done(null, false, error);
});
}
);
constructor() {
this.router = Router();
this.init();
}
public init() {
this.router.use(cors());
this.router.post('/login', AuthController.login);
this.router.get(
'/login/azure',
passport.authenticate(this.azureAdOauth2, { session: false, prompt: 'select_account' })
);
this.router.get(
'/login/azure/return',
passport.authenticate(this.azureAdOauth2, {
session: false,
failureRedirect: `${process.env.CLIENT_UI}/login?status=failed`,
}),
(req: IGetUserAuthInfoRequest, res) => {
res.cookie('abyss_jwt', (req.user as any).token, {
httpOnly: false,
expires: new Date(Date.now() + 24 * 3600000),
}).redirect(process.env.CLIENT_UI + '/login?status=success');
}
);
this.router.put('/forgot-password/:email/', UserController.setVerificationToken);
this.router.put('/change-forgotten-password/:email/', UserController.changePasswordWithVerificationToken);
}
}
const userRoutes = new UserRouter();
userRoutes.init();
export default userRoutes.router;
- Log files (redact/remove sensitive information)
- Application settings (redact/remove sensitive information)
Environment
- Version of this library used: 0.0.4
- Version of the platform or framework used, if applicable: N/A
- Other relevant versions (language, server software, OS, browser): nodejs 12.18.3 + express on macOS
- Other modules/plugins/libraries that might be involved: N/A