BAP: 578
Title: Non-Fungible Agent (NFA) Token Standard
Status: Draft
Type: Application
Created: 2025-05-27
- [BAP-578: Non-Fungible Agent (NFA) Token Standard]
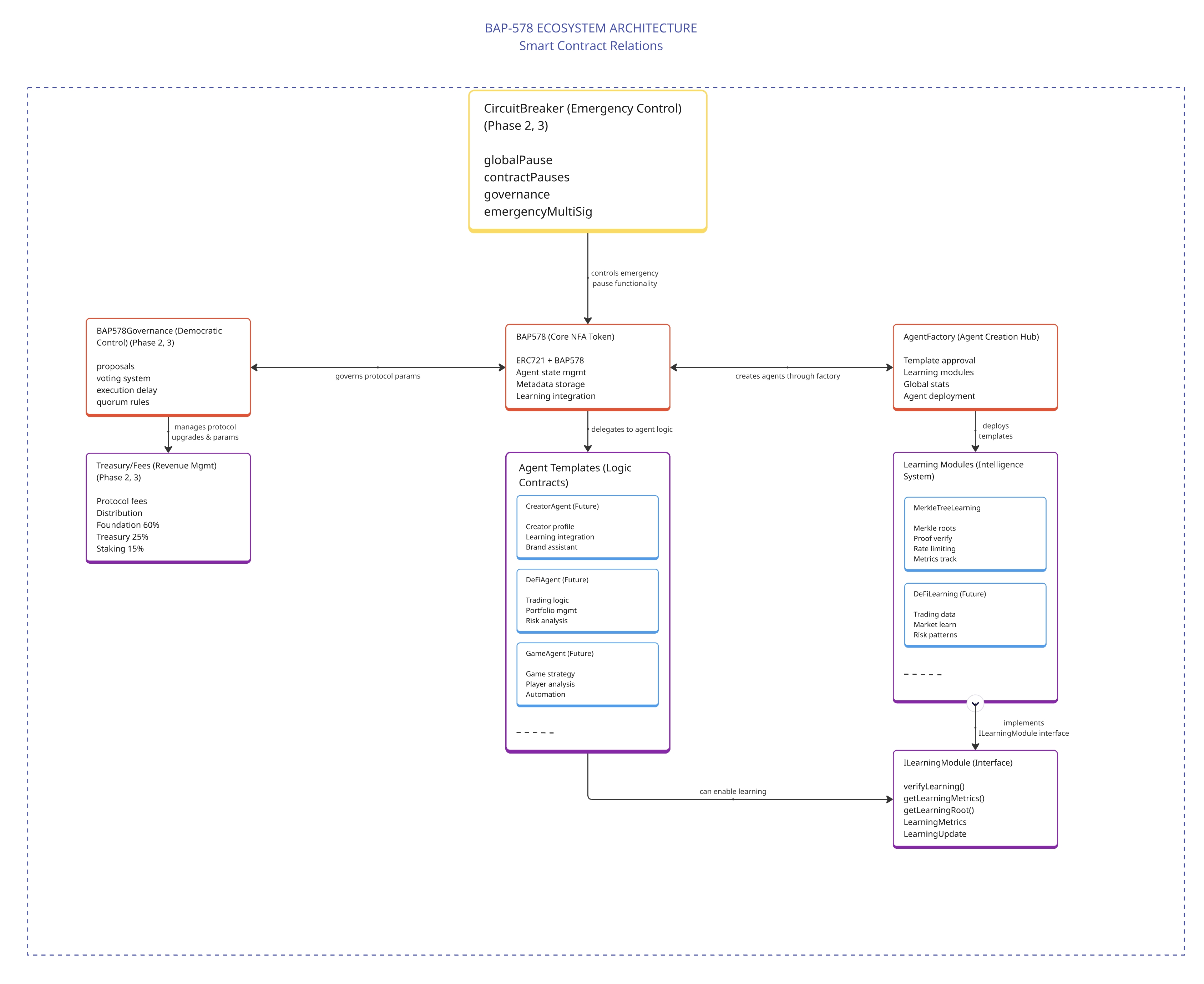
This BNB Chain Application (BAP) proposal, BAP-578, introduces the Non-Fungible Agent (NFA) token standard, extending ERC-721 to enable autonomous, intelligent digital entities with optional learning capabilities on BNB Chain. The standard provides a dual-path architecture supporting both traditional static agents and advanced learning-enabled agents, ensuring broad adoption while enabling cutting-edge AI capabilities.
A reference implementation is available here
BAP-578 defines a standardized framework for Non-Fungible Agents (NFAs) - intelligent, autonomous digital entities that combine the ownership guarantees of NFTs with the adaptive capabilities of artificial intelligence. This standard merges the uniqueness of NFTs with autonomous functionality, positioning BNB Chain as the home for decentralized automation.
The standard addresses the critical gap between traditional NFTs (which provide uniqueness and ownership) and the need for standardized interfaces that enable autonomous behavior and cross-platform agent interactions. BAP-578 provides a complete framework for creating, managing, and governing autonomous agent tokens with optional learning capabilities that allow agents to evolve and improve over time.
Key features include:
-
Dual-Path Architecture: Support for both JSON Light Memory (simple agents) and Merkle Tree Learning (evolving agents)
-
Cryptographically verfiable learning through Merkle Proofs:
-
NFAs employ a method-agnostic architecture that enables cryptographically verifiable learning through Merkle tree structures.
-
When users interact with an NFA, learning data, including preferences, patterns, confidence scores, and outcomes, is organized into a hierarchical tree structure.
-
This data progresses through a systematic process: interaction → learning extraction → tree building → Merkle root calculation → on-chain update.
-
Only the 32-byte Merkle root is stored on-chain, providing tamper-proof verification while preserving privacy and minimizing storage costs.
-
The flexible learning module architecture allows developers to implement various AI optimization methods.
-
Whether using RAG(leveraging off-chain vaults to retrieve past interactions), MCP (integrating with different AI providers through logic contracts), fine-tuning, reinforcement learning, or hybrid approaches, the BAP-578 standard provides the infrastructure without prescribing specific implementations.
-
Standardized Agent Lifecycle: Comprehensive lifecycle management from creation through evolution
-
Hybrid Storage Model: On-chain security with off-chain flexibility for rich experiences
-
Composable Intelligence: Agents can interact and collaborate while maintaining individual identity
-
Comprehensive Security: Multi-layer security framework with circuit breakers and access controls
-
Backward Compatibility: Full compatibility with existing ERC-721 infrastructure
While traditional NFTs (BEP-721) provide uniqueness and ownership, they lack the standardized interfaces needed for autonomous behavior and cross-platform agent interactions. The current blockchain ecosystem lacks standardization for intelligent, autonomous digital entities, creating several critical challenges that BAP-578 addresses.
BAP-578 defines standardized methods for action execution, state management, and logic upgrades that enable predictable interactions across platforms. Without this standardization, every intelligent token implementation requires custom integration work, forcing developers to learn new APIs and build specialized infrastructure for each project.
The standard establishes common patterns for how agents interact with other contracts, services, and each other, creating an ecosystem where agents from different developers can work together. This prevents the creation of isolated ecosystems that limit user choice and prevent network effects that drive innovation.
BAP-578 provides clear separation between on-chain identity and permissions versus off-chain extended memory and complex behaviors, optimizing for both gas efficiency and rich functionality. This hybrid approach ensures that critical security and identity information is secured by blockchain consensus while keeping gas costs reasonable for agent operations.
The standard includes standardized interfaces for agent learning and evolution, allowing developers to choose between simple static agents or sophisticated learning agents. This addresses the lack of learning standardization that has made it impossible for agents to share knowledge or for the ecosystem to benefit from collective intelligence.
BAP-578 establishes standardized circuit breaker patterns, permission systems, and access controls that protect users and their assets, replacing the patchwork of security models that are difficult to audit and trust.
Every intelligent token implementation requires custom integration work, significantly increasing development costs and time-to-market. Developers must learn new APIs and build specialized infrastructure for each project, preventing the ecosystem from benefiting from shared infrastructure.
Agents created on one platform cannot easily interact with agents from other platforms, creating isolated ecosystems that limit user choice and prevent network effects that drive innovation.
Each implementation uses different approaches to permissions and security, creating a patchwork of security models that are difficult to audit and trust.
Users become locked into specific platforms, unable to migrate their intelligent agents or leverage their accumulated learning across different applications.
There has been no standardized approach to enabling agents to learn and evolve, making it impossible for agents to carry their knowledge and experience across different platforms and applications.
BAP-578 carefully balances which components belong on-chain versus off-chain to optimize for security, cost-effectiveness, and functionality:
| Component | Storage | Rationale |
|---|---|---|
| Agent Identity | On-chain | Core identity must be immutable and universally accessible |
| Ownership & Permissions | On-chain | Security and access control require consensus verification |
| Basic Metadata | On-chain | Essential for marketplace display and basic interactions |
| Logic Address | On-chain | Determines how the agent behaves when actions are executed |
| Learning Tree Root | On-chain | Cryptographic proof of learning state (32 bytes only) |
| Extended Memory | Off-chain (with hash verification) | Rich memory would be prohibitively expensive on-chain |
| Learning Tree Data | Off-chain (with Merkle verification) | Detailed learning data with cryptographic integrity |
| Complex Behaviors | Off-chain | Advanced AI behaviors require off-chain computation |
| Voice/Animation | Off-chain (with URI reference) | Media assets are too large for on-chain storage |
This hybrid approach ensures that:
- Critical security and identity information is secured by blockchain consensus
- Gas costs remain reasonable for agent operations
- Rich agent experiences can evolve without blockchain limitations
- Learning capabilities are cryptographically verifiable yet cost-efficient
BAP-578 addresses these challenges by providing:
- Universal Compatibility: Standardized interfaces that work across all platforms
- User Ownership: True ownership of intelligent agents and their accumulated knowledge
- Ecosystem Interoperability: Agents that maintain consistent behavior across applications
- Innovation Acceleration: Shared infrastructure that enables focus on unique value creation
- Future-Ready Design: Architecture that supports both current needs and future AI advances
The BAP-578 standard extends ERC-721 with agent-specific functionality:
interface IBAP578 {
enum Status { Active, Paused, Terminated }
struct State {
uint256 balance;
Status status;
address owner;
address logicAddress;
uint256 lastActionTimestamp;
}
struct AgentMetadata {
string persona; // JSON-encoded character traits
string experience; // Agent's role/purpose summary
string voiceHash; // Audio profile reference
string animationURI; // Animation/avatar URI
string vaultURI; // Extended data storage URI
bytes32 vaultHash; // Vault content verification hash
}
// Events
event ActionExecuted(address indexed agent, bytes result);
event LogicUpgraded(address indexed agent, address oldLogic, address newLogic);
event AgentFunded(address indexed agent, address indexed funder, uint256 amount);
event StatusChanged(address indexed agent, Status newStatus);
event MetadataUpdated(uint256 indexed tokenId, string metadataURI);
// Core Functions
function executeAction(uint256 tokenId, bytes calldata data) external;
function setLogicAddress(uint256 tokenId, address newLogic) external;
function fundAgent(uint256 tokenId) external payable;
function getState(uint256 tokenId) external view returns (State memory);
function getAgentMetadata(uint256 tokenId) external view returns (AgentMetadata memory);
function updateAgentMetadata(uint256 tokenId, AgentMetadata memory metadata) external;
// Lifecycle Management
function pause(uint256 tokenId) external;
function unpause(uint256 tokenId) external;
function terminate(uint256 tokenId) external;
}Agents maintain state information that tracks their operational status, balance, and activity:
struct State {
uint256 balance; // BNB balance for gas fees
Status status; // Current operational status
address owner; // Agent owner address
address logicAddress; // Logic contract address
uint256 lastActionTimestamp; // Last action execution time
}Status Management:
Active: Agent can execute actions and interact normallyPaused: Agent is temporarily suspended but can be resumedTerminated: Agent is permanently disabled with balance returned to owner
BAP-578 extends standard ERC-721 metadata with agent-specific fields to support both simple and learning agents:
struct AgentMetadata {
string persona; // JSON-encoded character traits, style, tone
string experience; // Short summary of agent's role/purpose
string voiceHash; // Reference ID to stored audio profile
string animationURI; // URI to video or animation file
string vaultURI; // URI to agent's vault (extended data storage)
bytes32 vaultHash; // Hash of vault contents for verification
}struct EnhancedAgentMetadata {
// Core fields (inherited from AgentMetadata)
string persona;
string experience;
string voiceHash;
string animationURI;
string vaultURI;
bytes32 vaultHash;
// Learning-specific fields
bool learningEnabled; // Learning capability flag
address learningModule; // Learning module contract address
bytes32 learningTreeRoot; // Merkle root of learning tree
uint256 learningVersion; // Learning implementation version
uint256 lastLearningUpdate; // Timestamp of last learning update
}The learning module system provides standardized interfaces for implementing different learning algorithms:
interface ILearningModule {
struct LearningMetrics {
uint256 totalInteractions; // Total user interactions
uint256 learningEvents; // Significant learning updates
uint256 lastUpdateTimestamp; // Last learning update time
uint256 learningVelocity; // Learning rate (scaled by 1e18)
uint256 confidenceScore; // Overall confidence (scaled by 1e18)
}
struct LearningUpdate {
bytes32 previousRoot; // Previous Merkle root
bytes32 newRoot; // New Merkle root
bytes32 proof; // Merkle proof for update
bytes32 metadata; // Encoded learning data
}
function updateLearning(uint256 tokenId, LearningUpdate calldata update) external;
function verifyLearning(uint256 tokenId, bytes32 claim, bytes32[] calldata proof) external view returns (bool);
function getLearningMetrics(uint256 tokenId) external view returns (LearningMetrics memory);
function getLearningRoot(uint256 tokenId) external view returns (bytes32);
function isLearningEnabled(uint256 tokenId) external view returns (bool);
function getVersion() external pure returns (string memory);
function recordInteraction(uint256 tokenId, string calldata interactionType, bool success) external;
}Learning data is organized in a hierarchical tree structure with on-chain verification:
- On-Chain Storage: Only the Merkle root (32 bytes) is stored on-chain
- Off-Chain Storage: Full learning tree stored in user-controlled vaults
- Cryptographic Verification: All learning claims verified through Merkle proofs
- Gas Efficiency: Minimal on-chain storage with full verification capabilities
The memory module registry allows agents to register external memory sources:
interface IMemoryModuleRegistry {
struct MemoryModule {
address moduleAddress;
string metadata;
bytes32 metadataHash;
uint256 registrationTime;
bool isActive;
}
function registerModule(
uint256 tokenId,
address moduleAddress,
string memory metadata,
bytes memory signature
) external;
function verifyModule(
uint256 tokenId,
address moduleAddress,
bytes32 expectedHash
) external view returns (bool);
function getModule(uint256 tokenId, address moduleAddress)
external view returns (MemoryModule memory);
}The vault permission system manages access to off-chain agent data:
interface IVaultPermissionManager {
enum PermissionLevel { READ_ONLY, WRITE, ADMIN, FULL_CONTROL }
struct Permission {
address delegate;
PermissionLevel level;
uint256 expiryTime;
bool isActive;
}
function delegateAccess(
uint256 tokenId,
address delegate,
PermissionLevel level,
uint256 expiryTime,
bytes memory signature
) external;
function revokeAccess(uint256 tokenId, address delegate) external;
function verifyAccess(uint256 tokenId, address accessor, PermissionLevel requiredLevel)
external view returns (bool);
}interface ICircuitBreaker {
function pauseGlobally() external;
function pauseContract(address contractAddress) external;
function pauseAgent(uint256 tokenId) external;
function unpauseGlobally() external;
function unpauseContract(address contractAddress) external;
function unpauseAgent(uint256 tokenId) external;
function isGloballyPaused() external view returns (bool);
function isContractPaused(address contractAddress) external view returns (bool);
function isAgentPaused(uint256 tokenId) external view returns (bool);
}- Owner-Only Operations: Critical functions restricted to agent owner
- Governance Controls: System-wide parameters managed by governance
- Time-Based Permissions: Temporary access delegation with automatic expiry
- Cryptographic Verification: Signature-based verification for sensitive operations
uint256 public constant MAX_GAS_FOR_DELEGATECALL = 3000000;
uint256 public constant MAX_GAS_FOR_LEARNING_UPDATE = 500000;BAP-578 includes a template system for specialized agent types:
interface IAgentTemplate {
function getTemplateInfo() external view returns (
string memory name,
string memory description,
uint256 version,
bytes32 codeHash
);
function initialize(uint256 tokenId, bytes memory initData) external;
function getCapabilities() external view returns (string[] memory);
}- DeFiAgent: Specialized for DeFi operations and trading
- GameAgent: Optimized for gaming and virtual world interactions
- DAOAgent: Designed for governance and DAO participation
- CreatorAgent: Focused on content creation and artistic endeavors
- StrategicAgent: Built for analysis and strategic decision-making
BAP-578 offers two development paths to accommodate different use cases and developer preferences:
Perfect for most developers and immediate deployment:
- Simple: Familiar JSON metadata approach (like standard NFTs)
- Fast: Deploy agents immediately with no complexity
- Compatible: Works with all existing NFT infrastructure
- Cost-effective: Minimal gas costs for basic operations
For advanced developers wanting truly evolving agents:
- Evolving: Agents that genuinely learn and improve over time
- Provable: Cryptographically verifiable learning history
- Efficient: Only 32-byte Merkle roots stored on-chain
- Advanced: Cutting-edge AI agent capabilities from day 1
- Backward Compatibility: All existing agents continue working unchanged
- Optional Adoption: Choose your complexity level
- Upgrade Path: Simple agents can enable learning later
- Gas Optimized: Learning data stored off-chain with on-chain verification
- Future-Proof: Architecture supports advanced AI developments
The dual-path approach (JSON Light Memory vs. Merkle Tree Learning) ensures broad adoption by providing immediate utility while enabling advanced capabilities for users ready to embrace AI features. This design allows developers to start simple and upgrade to learning capabilities when needed.
Storing critical identity on-chain while keeping detailed data off-chain optimizes for both security and cost-effectiveness. This approach ensures that essential security and identity information is secured by blockchain consensus while keeping gas costs reasonable for agent operations.
Pluggable learning modules allow for different algorithms and future upgrades without breaking existing functionality. This modularity enables the ecosystem to evolve and adopt new learning techniques as they become available.
Using Merkle trees for learning data provides cryptographic verification while minimizing on-chain storage costs. This approach enables verifiable learning with only 32 bytes of on-chain storage per agent.
The emphasis on standardization addresses the critical gap in the current ecosystem where every intelligent token implementation requires custom integration work, preventing ecosystem-wide benefits and interoperability.
Rejected due to prohibitive gas costs for rich agent data and learning information. The hybrid approach provides the security benefits of on-chain storage for critical data while maintaining cost-effectiveness.
Rejected to maintain decentralization and user ownership principles. The Merkle tree approach provides verifiable learning while maintaining user control over their agent's data.
Rejected to ensure broad adoption across different user comfort levels with AI technology. The dual-path approach accommodates both simple use cases and advanced AI capabilities.
Rejected in favor of standardization to prevent ecosystem fragmentation and enable universal compatibility across platforms and applications.
BAP-578 is fully backwards compatible with ERC-721:
- All ERC-721 functions remain unchanged
- Existing NFT marketplaces can list BAP-578 tokens
- Standard NFT wallets can hold and transfer BAP-578 tokens
- Additional functionality is opt-in and doesn't affect basic operations
- Simple agents using JSON Light Memory work exactly like traditional NFTs
- Learning capabilities can be enabled later without breaking existing functionality
// Test agent creation
function testAgentCreation() public {
uint256 tokenId = bap578.createAgent(
user,
logicAddress,
"ipfs://metadata",
basicMetadata
);
assertEq(bap578.ownerOf(tokenId), user);
assertEq(bap578.getState(tokenId).status, Status.Active);
}
// Test action execution
function testActionExecution() public {
bytes memory data = abi.encodeWithSignature("performAction()");
bap578.executeAction(tokenId, data);
// Verify action was executed
assertTrue(actionExecuted);
}// Test learning update
function testLearningUpdate() public {
LearningUpdate memory update = LearningUpdate({
previousRoot: currentRoot,
newRoot: newRoot,
proof: merkleProof,
metadata: learningData
});
learningModule.updateLearning(tokenId, update);
assertEq(learningModule.getLearningRoot(tokenId), newRoot);
}
// Test learning enablement
function testEnableLearning() public {
bytes32 initialRoot = keccak256("initial_learning_data");
bap578Enhanced.enableLearning(tokenId, learningModule.address, initialRoot);
assertTrue(bap578Enhanced.isLearningEnabled(tokenId));
}// Test unauthorized access prevention
function testUnauthorizedAccess() public {
vm.prank(unauthorizedUser);
vm.expectRevert("BAP578: caller is not agent owner");
bap578.executeAction(tokenId, data);
}
// Test circuit breaker
function testCircuitBreaker() public {
circuitBreaker.pauseGlobally();
vm.expectRevert("BAP578: global pause active");
bap578.executeAction(tokenId, data);
}// Test simple agent compatibility
function testSimpleAgentCompatibility() public {
// Create simple agent
uint256 simpleTokenId = bap578.createAgent(user, logicAddress, "ipfs://metadata", basicMetadata);
// Verify it works like standard NFT
assertEq(bap578.ownerOf(simpleTokenId), user);
assertFalse(bap578Enhanced.isLearningEnabled(simpleTokenId));
}
// Test learning upgrade path
function testLearningUpgradePath() public {
// Start with simple agent
uint256 tokenId = bap578.createAgent(user, logicAddress, "ipfs://metadata", basicMetadata);
// Enable learning later
bytes32 initialRoot = keccak256("initial_learning_data");
bap578Enhanced.enableLearning(tokenId, learningModule.address, initialRoot);
// Verify learning is now enabled
assertTrue(bap578Enhanced.isLearningEnabled(tokenId));
}A reference implementation is available at: https://github.com/ChatAndBuild/non-fungible-agents-BAP-578
The implementation includes:
- Core BAP-578 contract with full specification compliance
- Enhanced BAP-578 contract with learning capabilities
- Learning module implementations (Merkle tree, federated learning)
- Memory module registry
- Vault permission manager
- Circuit breaker system
- Agent factory for streamlined deployment
- Multiple agent templates for different use cases
- Dual-path architecture supporting both simple and learning agents
- Migration tools for upgrading simple agents to learning agents
- Reentrancy Protection: All fund-handling functions use ReentrancyGuard
- Access Control: Strict permissions for sensitive operations
- Gas Limits: Prevent out-of-gas attacks on delegatecall operations
- Circuit Breakers: Emergency pause mechanisms for rapid incident response
- Rate Limiting: Prevent spam and gaming of learning systems (maximum 50 learning updates per day per agent)
- Cryptographic Verification: All learning claims must be provable through Merkle proofs
- Module Approval: Only governance-approved learning modules allowed
- Privacy Protection: Learning data access is controlled and auditable
- Tamper-Proof History: Learning history cannot be falsified due to cryptographic verification
- Agent Funding: Agents must maintain balance for gas fees
- Owner Controls: Only owners can modify critical agent parameters
- Governance Oversight: System parameters controlled by decentralized governance
- Vault Permissions: Granular access control for off-chain data
- Signature Verification: Cryptographic verification for sensitive operations
- Hash Verification: Content integrity verification for off-chain data
- Time-Based Access: Delegated permissions with automatic expiry
- Backward Compatibility: Simple agents maintain all existing security guarantees
- Optional Complexity: Learning features are opt-in and don't affect simple agent security
- Upgrade Safety: Enabling learning on existing agents doesn't compromise existing functionality
The content is licensed under CC0.