|
| 1 | +# Knative Canary Deployments |
| 2 | + |
| 3 | +This guide shows you how to use [Knative](https://knative.dev/) and Flagger to automate canary deployments. |
| 4 | + |
| 5 | +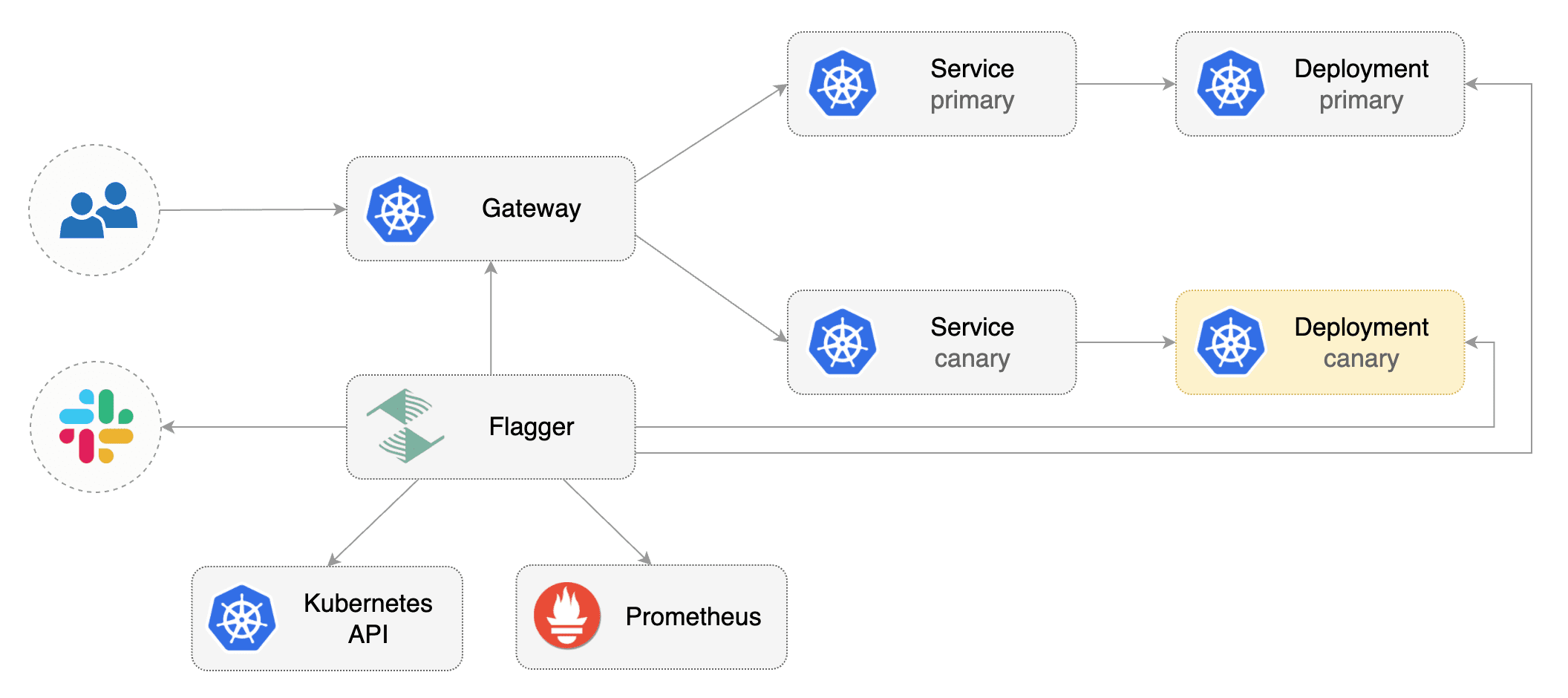 |
| 6 | + |
| 7 | +## Prerequisites |
| 8 | + |
| 9 | +Flagger requires a Kubernetes cluster **v1.19** or newer and a Knative Serving installation that supports |
| 10 | +the resources with `serving.knative.dev/v1` as their API version. |
| 11 | + |
| 12 | +Install Knative v1.17.0: |
| 13 | + |
| 14 | +```bash |
| 15 | +kubectl apply -f https://github.com/knative/serving/releases/download/knative-v1.17.0/serving-crds.yaml |
| 16 | +kubectl apply -f https://github.com/knative/serving/releases/download/knative-v1.17.0/serving-core.yaml |
| 17 | +kubectl apply -f https://github.com/knative/net-kourier/releases/download/knative-v1.17.0/kourier.yaml |
| 18 | +kubectl patch configmap/config-network \ |
| 19 | + --namespace knative-serving \ |
| 20 | + --type merge \ |
| 21 | + --patch '{"data":{"ingress-class":"kourier.ingress.networking.knative.dev"}}' |
| 22 | +``` |
| 23 | + |
| 24 | + |
| 25 | +Install Flagger in the `flagger-system` namespace: |
| 26 | + |
| 27 | +```bash |
| 28 | +kubectl apply -k github.com/fluxcd/flagger//kustomize/knative |
| 29 | +``` |
| 30 | + |
| 31 | +Create a namespace for your Kntive Service: |
| 32 | + |
| 33 | +```bash |
| 34 | +kubectl create namespace test |
| 35 | +``` |
| 36 | + |
| 37 | +Create a Knative Service that deploys podinfo: |
| 38 | + |
| 39 | +```yaml |
| 40 | +apiVersion: serving.knative.dev/v1 |
| 41 | +kind: Service |
| 42 | +metadata: |
| 43 | + name: podinfo |
| 44 | + namespace: test |
| 45 | +spec: |
| 46 | + template: |
| 47 | + spec: |
| 48 | + containers: |
| 49 | + - image: ghcr.io/stefanprodan/podinfo:6.0.0 |
| 50 | + ports: |
| 51 | + - containerPort: 9898 |
| 52 | + protocol: TCP |
| 53 | + command: |
| 54 | + - ./podinfo |
| 55 | + - --port=9898 |
| 56 | + - --port-metrics=9797 |
| 57 | + - --grpc-port=9999 |
| 58 | + - --grpc-service-name=podinfo |
| 59 | + - --level=info |
| 60 | + - --random-delay=false |
| 61 | + - --random-error=false |
| 62 | +``` |
| 63 | +
|
| 64 | +Deploy the load testing service to generate traffic during the canary analysis: |
| 65 | +
|
| 66 | +```bash |
| 67 | +kubectl apply -k https://github.com/fluxcd/flagger//kustomize/tester?ref=main |
| 68 | +``` |
| 69 | + |
| 70 | +Create a Canary custom resource: |
| 71 | + |
| 72 | +```yaml |
| 73 | +apiVersion: flagger.app/v1beta1 |
| 74 | +kind: Canary |
| 75 | +metadata: |
| 76 | + name: podinfo |
| 77 | + namespace: test |
| 78 | +spec: |
| 79 | + provider: knative |
| 80 | + # knative service ref |
| 81 | + targetRef: |
| 82 | + apiVersion: serving.knative.dev/v1 |
| 83 | + kind: Service |
| 84 | + name: podinfo |
| 85 | + # the maximum time in seconds for the canary deployment |
| 86 | + # to make progress before it is rollback (default 600s) |
| 87 | + progressDeadlineSeconds: 60 |
| 88 | + analysis: |
| 89 | + # schedule interval (default 60s) |
| 90 | + interval: 15s |
| 91 | + # max number of failed metric checks before rollback |
| 92 | + threshold: 15 |
| 93 | + # max traffic percentage routed to canary |
| 94 | + maxWeight: 50 |
| 95 | + # canary increment step |
| 96 | + # percentage (0-100) |
| 97 | + stepWeight: 10 |
| 98 | + metrics: |
| 99 | + - name: request-success-rate |
| 100 | + # min success rate (non-5xx responses) |
| 101 | + # percentage (0-100) |
| 102 | + thresholdRange: |
| 103 | + min: 99 |
| 104 | + interval: 1m |
| 105 | + - name: request-duration |
| 106 | + # milliseconds |
| 107 | + thresholdRange: |
| 108 | + max: 500 |
| 109 | + interval: 1m |
| 110 | + webhooks: |
| 111 | + - name: load-test |
| 112 | + url: http://flagger-loadtester.test/ |
| 113 | + timeout: 5s |
| 114 | + metadata: |
| 115 | + type: cmd |
| 116 | + cmd: "hey -z 1m -q 5 -c 2 http://podinfo.test" |
| 117 | + logCmdOutput: "true" |
| 118 | +``` |
| 119 | +
|
| 120 | +> Note: Please note that for a Canary resource with `.spec.provider` set to `knative`, the resource is only valid if the |
| 121 | +`.spec.targetRef.kind` is `Service` and `.spec.targetRef.apiVersion` is `serving.knative.dev/v1`. |
| 122 | + |
| 123 | +Save the above resource as podinfo-canary.yaml and then apply it: |
| 124 | + |
| 125 | +```bash |
| 126 | +kubectl apply -f ./podinfo-canary.yaml |
| 127 | +``` |
| 128 | + |
| 129 | +When the canary analysis starts, Flagger will call the pre-rollout webhooks before routing traffic to the canary. |
| 130 | +The canary analysis will run for five minutes while validating the HTTP metrics and rollout hooks every minute. |
| 131 | + |
| 132 | +After a couple of seconds Flagger will make the following changes the Knative Service `podinfo`: |
| 133 | + |
| 134 | +* Add an annotation to the object with the name `flagger.app/primary-revision`. |
| 135 | +* Modify the `.spec.traffic` section of the object such that it can manipulate the traffic spread between |
| 136 | + the primary and canary Knative Revision. |
| 137 | + |
| 138 | +## Automated canary promotion |
| 139 | + |
| 140 | +Trigger a canary deployment by updating the container image: |
| 141 | + |
| 142 | +```bash |
| 143 | +kubectl -n test set image deployment/podinfo \ |
| 144 | +podinfod=stefanprodan/podinfo:6.0.1 |
| 145 | +``` |
| 146 | + |
| 147 | +Flagger detects that the deployment revision changed and starts a new rollout: |
| 148 | + |
| 149 | +```text |
| 150 | +kubectl -n test describe canary/podinfo |
| 151 | +
|
| 152 | +Status: |
| 153 | + Canary Weight: 0 |
| 154 | + Failed Checks: 0 |
| 155 | + Phase: Succeeded |
| 156 | +Events: |
| 157 | + Type Reason Age From Message |
| 158 | + ---- ------ ---- ---- ------- |
| 159 | + Normal Synced 3m flagger New revision detected podinfo.test |
| 160 | + Normal Synced 3m flagger Scaling up podinfo.test |
| 161 | + Warning Synced 3m flagger Waiting for podinfo.test rollout to finish: 0 of 1 updated replicas are available |
| 162 | + Normal Synced 3m flagger Advance podinfo.test canary weight 5 |
| 163 | + Normal Synced 3m flagger Advance podinfo.test canary weight 10 |
| 164 | + Normal Synced 3m flagger Advance podinfo.test canary weight 15 |
| 165 | + Normal Synced 2m flagger Advance podinfo.test canary weight 20 |
| 166 | + Normal Synced 2m flagger Advance podinfo.test canary weight 25 |
| 167 | + Normal Synced 1m flagger Advance podinfo.test canary weight 30 |
| 168 | + Normal Synced 1m flagger Advance podinfo.test canary weight 35 |
| 169 | + Normal Synced 55s flagger Advance podinfo.test canary weight 40 |
| 170 | + Normal Synced 45s flagger Advance podinfo.test canary weight 45 |
| 171 | + Normal Synced 35s flagger Advance podinfo.test canary weight 50 |
| 172 | + Normal Synced 25s flagger Copying podinfo.test template spec to podinfo-primary.test |
| 173 | + Warning Synced 15s flagger Waiting for podinfo-primary.test rollout to finish: 1 of 2 updated replicas are available |
| 174 | + Normal Synced 5s flagger Promotion completed! Scaling down podinfo.test |
| 175 | +``` |
| 176 | + |
| 177 | +**Note** that if you apply new changes to the deployment during the canary analysis, Flagger will restart the analysis. |
| 178 | + |
| 179 | +A canary deployment is triggered by changes in any of the following objects: |
| 180 | + |
| 181 | +* Deployment PodSpec \(container image, command, ports, env, resources, etc\) |
| 182 | +* ConfigMaps mounted as volumes or mapped to environment variables |
| 183 | +* Secrets mounted as volumes or mapped to environment variables |
| 184 | + |
| 185 | +You can monitor how Flagger progressively changes the Knative Service object to spread traffic between Knative Revisions: |
| 186 | + |
| 187 | +```bash |
| 188 | +watch kubectl get httproute -n test podinfo -o=jsonpath='{.spec.traffic}' |
| 189 | +``` |
| 190 | + |
| 191 | +You can monitor all canaries with: |
| 192 | + |
| 193 | +```bash |
| 194 | +watch kubectl get canaries --all-namespaces |
| 195 | +
|
| 196 | +NAMESPACE NAME STATUS WEIGHT LASTTRANSITIONTIME |
| 197 | +test podinfo Progressing 15 2022-01-16T14:05:07Z |
| 198 | +prod frontend Succeeded 0 2022-01-15T16:15:07Z |
| 199 | +prod backend Failed 0 2022-01-14T17:05:07Z |
| 200 | +``` |
| 201 | + |
| 202 | +## Automated rollback |
| 203 | + |
| 204 | +During the canary analysis you can generate HTTP 500 errors and high latency to test if Flagger pauses the rollout. |
| 205 | + |
| 206 | +Trigger another canary deployment: |
| 207 | + |
| 208 | +```bash |
| 209 | +kubectl -n test set image deployment/podinfo \ |
| 210 | +podinfod=stefanprodan/podinfo:6.0.2 |
| 211 | +``` |
| 212 | + |
| 213 | +Exec into the load tester pod with: |
| 214 | + |
| 215 | +```bash |
| 216 | +kubectl -n test exec -it flagger-loadtester-xx-xx sh |
| 217 | +``` |
| 218 | + |
| 219 | +Generate HTTP 500 errors: |
| 220 | + |
| 221 | +```bash |
| 222 | +watch curl http://podinfo-canary:9898/status/500 |
| 223 | +``` |
| 224 | + |
| 225 | +Generate latency: |
| 226 | + |
| 227 | +```bash |
| 228 | +watch curl http://podinfo-canary:9898/delay/1 |
| 229 | +``` |
| 230 | + |
| 231 | +When the number of failed checks reaches the canary analysis threshold, the traffic is routed back to the primary, the canary is scaled to zero and the rollout is marked as failed. |
| 232 | + |
| 233 | +```text |
| 234 | +kubectl -n test describe canary/podinfo |
| 235 | +
|
| 236 | +Status: |
| 237 | + Canary Weight: 0 |
| 238 | + Failed Checks: 10 |
| 239 | + Phase: Failed |
| 240 | +Events: |
| 241 | + Type Reason Age From Message |
| 242 | + ---- ------ ---- ---- ------- |
| 243 | + Normal Synced 3m flagger Starting canary deployment for podinfo.test |
| 244 | + Normal Synced 3m flagger Advance podinfo.test canary weight 5 |
| 245 | + Normal Synced 3m flagger Advance podinfo.test canary weight 10 |
| 246 | + Normal Synced 3m flagger Advance podinfo.test canary weight 15 |
| 247 | + Normal Synced 3m flagger Halt podinfo.test advancement error rate 69.17% > 1% |
| 248 | + Normal Synced 2m flagger Halt podinfo.test advancement error rate 61.39% > 1% |
| 249 | + Normal Synced 2m flagger Halt podinfo.test advancement error rate 55.06% > 1% |
| 250 | + Normal Synced 2m flagger Halt podinfo.test advancement error rate 47.00% > 1% |
| 251 | + Normal Synced 2m flagger (combined from similar events): Halt podinfo.test advancement error rate 38.08% > 1% |
| 252 | + Warning Synced 1m flagger Rolling back podinfo.test failed checks threshold reached 10 |
| 253 | + Warning Synced 1m flagger Canary failed! Scaling down podinfo.test |
| 254 | +``` |
0 commit comments