Malware and listener created with python
still under development
Features:
>Remote Access through shell
>keglogging
>grab chrome passwords
>registry persistence
>upload and download files
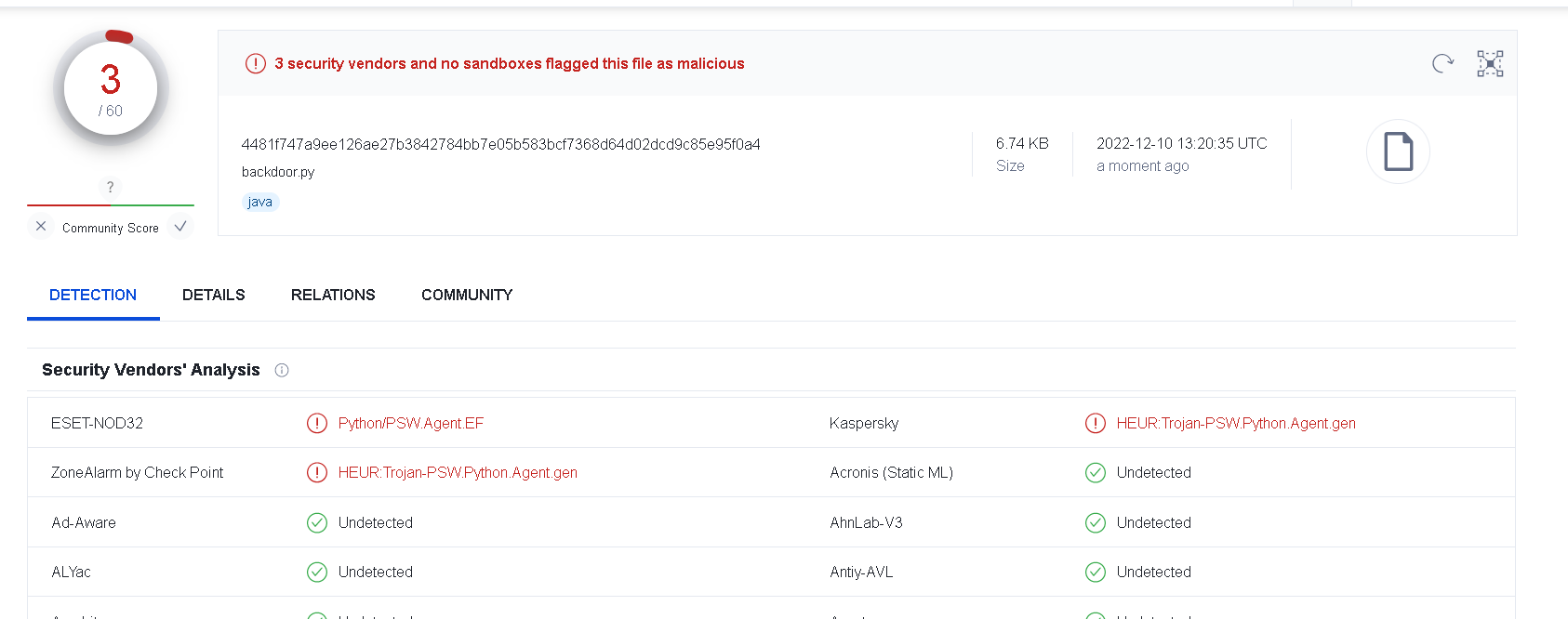
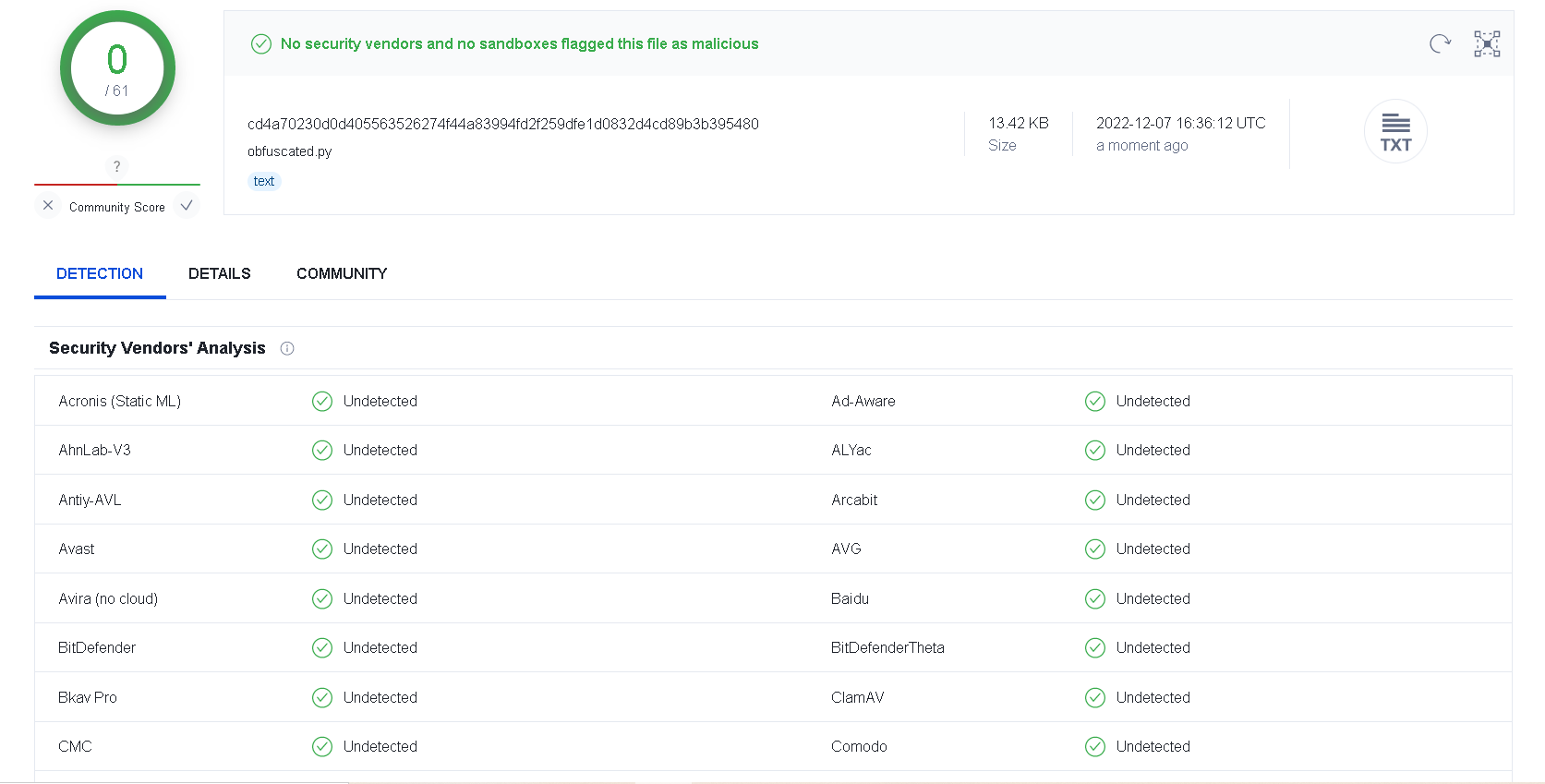
>undetectable
>screenshot
>checkprivilege
>grab discord token(through webhook)
Upcoming features:
grab wifi passwords
grab windows product key
privilege escalation technique
C2 listener
How to use?
1. edit the host and the port for the listener.py and the backdoor.py
optional: put your webhook in the discord.py file to recieve discord token
2. install the requirements.txt using "pip3 install -r requirements.txt"
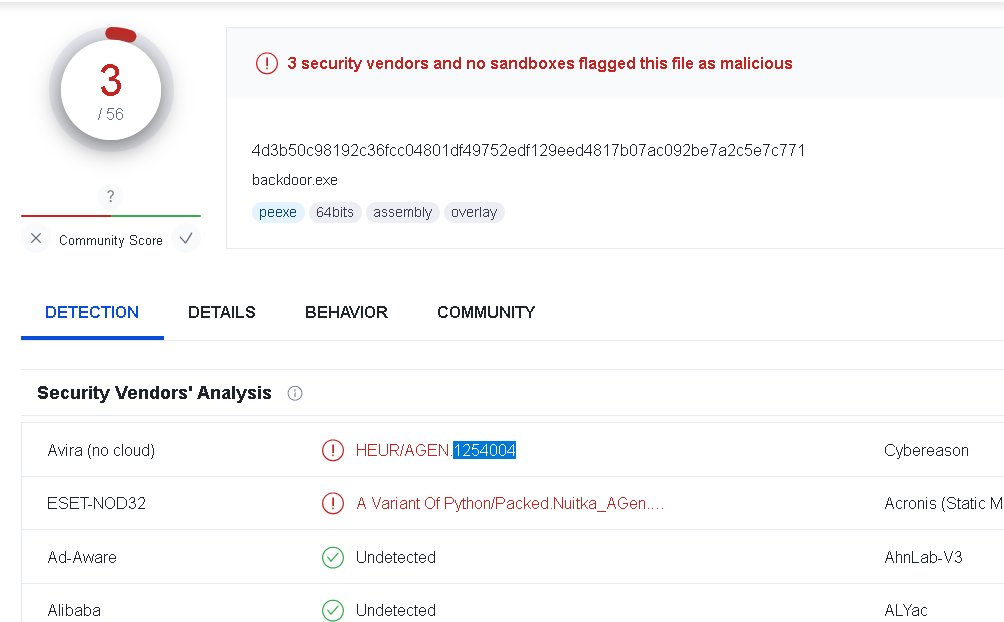
3. and then "compile" the backdoor.py and the keylogger.py using pyinstaller or nuitka to create the payload
4. start the listener.py on your target machine and execute the payload on your victime machine
Note: For those braindead people , the plain obfuscated python file is non detectable , however depending on how you convert the python code to an exe, the exe may not be fully undetectable
python to exe detection (nuitka):
Evading Bitdefender example:
evade.bit.mp4
.
.
. join my discord for more enquiries https://discord.gg/3R3BaDrTPK