-
Notifications
You must be signed in to change notification settings - Fork 21
Open
Description
Hey Folks - appreciate you guys creating this, we have had a lot of success using it, and hope to release a open production-ready setup example sometime this year :)
I noticed that currently, the orthanc client does not need a client secret to login. This confused me for a couple of reasons:
- Why is it needed for the Orthanc 2 UI, as specified here
- Why was this decision made? Apologies if I am missing something, I don't have much experience with this side of cyber security - I've hacked together this knowledge with google searches this afternoon.
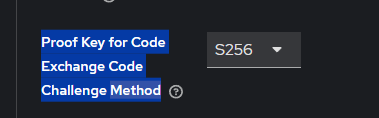
As well as this, I noticed that Proof Key for Code Exchange Code Challenge Method is set to plain
And that the public client access type is enabled by default
From the little I know, I imagine we should enforce S256 by default, and leave the public access type enabled, since I think the orthanc auth service uses S256 already. By changing the Code Challenge Method we stop other services from authenticating and doing weird token manipulation.
Thanks!
Reactions are currently unavailable
Metadata
Metadata
Assignees
Labels
No labels