|
5 | 5 | [](https://opensource.org/licenses/GPL-3.0/) |
6 | 6 | [](https://github.com/ellerbrock/open-source-badges/) |
7 | 7 |
|
8 | | -# [中文](README_ZH.md) |
| 8 | +Engilish|[🇨🇳中文](README_ZH.md) |
9 | 9 |
|
10 | | -# Changelog in 16/04/2018 |
| 10 | +## goproxy |
11 | 11 |
|
12 | | -## Change redis client |
13 | | -Change the redis client in goproxy from radix.v2 to redigo. |
| 12 | +goproxy is a load-balancing, reverse-proxy server implemented in go, supporting cache( by redis). As a load-balancing server, it supports 4 algorithms: Randomized Algorithm, Weight Round Robin Algorithm, Power of Two Choices (P2C) Algorithm, IP Hash Algorithm, Consistent Hashing with Bounded Loads Algorithm, besides, goproxy can dominate the http requests: filtering and blocking specific requests and even rewriting them. |
14 | 13 |
|
15 | | -Reason: |
| 14 | +Sometimes your program needs to call some third party API and wants to customize the responses from it, in that case, goproxy will be your great choice. |
16 | 15 |
|
17 | | ->There is a potential issue in the connection pool of radix.v2 which generates new connection to redis even though the current number of connections exceeds the maximum size of radix.v2 pool and this implementation may led to the redis cluster collapse. |
18 | | -> |
19 | | ->I had tried to submit a PR to radix.v2 expecting to fix it but the author from radix.v2 rejected that PR saying that logic in radix.v2 pool was intended..., well, he is the author of radix.v2 so he got the right to determine what radix.v2 should be. However, based on the conflicting ideas from us, I'm afraid I have to change the redis client in goproxy from radix.v2 to redigo whose connection pool will restrict the size of connections severely. |
| 16 | +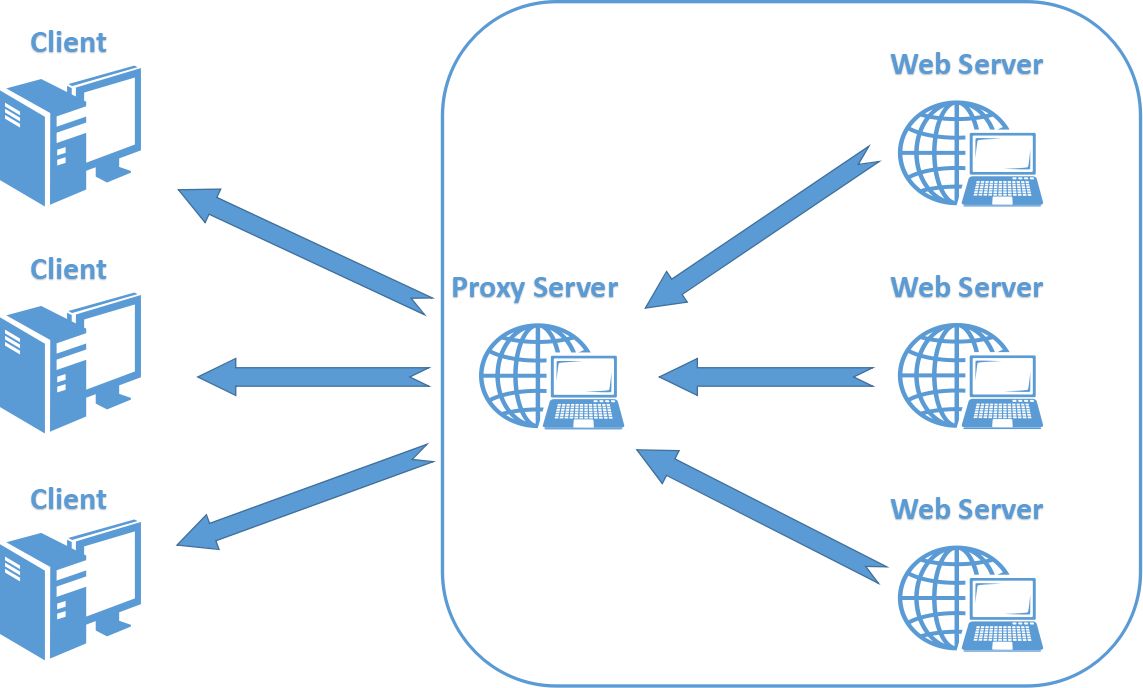 |
20 | 17 |
|
21 | | -# Changelog in 11/02/2018 |
22 | | -## Optimization in configurations management of goproxy |
| 18 | +## 🚀 Features: |
23 | 19 |
|
24 | | ->Managing configurations in goproxy with [viper](https://github.com/spf13/viper) which supports eager loading and means it will take effect immediately right after you update the configuration file. |
25 | | -
|
26 | | -# Changelog in 22/07/2017 |
27 | | -## Add 4 new algorithms into goproxy for load balancing: |
28 | | - |
29 | | -* Round Robin Algorithm |
30 | | -* Weight Round Robin Algorithm |
31 | | -* Power of Two Choices (P2C) Algorithm |
32 | | -* Consistent Hashing with Bounded Loads Algorithm |
33 | | - |
34 | | - |
35 | | -# goproxy |
36 | | ->goproxy is a load-balancing, reverse-proxy server implemented in go, supporting cache( by redis). As a load-balancing server, it supports 4 algorithms: Randomized Algorithm, Weight Round Robin Algorithm, Power of Two Choices (P2C) Algorithm, IP Hash Algorithm, Consistent Hashing with Bounded Loads Algorithm, besides, goproxy can dominate the http requests: filtering and blocking specific requests and even rewriting them. |
37 | | -> |
38 | | ->Sometimes your program needs to call some third party API and wants to customize the responses from it, in that case, goproxy will be your great choice. |
39 | | -
|
40 | | -# Features: |
41 | | - |
42 | | -## 1.Reverse-proxy, load-balancing, 4 algorithms for load-balancing in goproxy |
43 | | - |
44 | | -- GET/POST/PUT/DELETE methods in http and CONNECT method in https are supported in goproxy |
45 | | -- Http authentication was also supported |
46 | | -- Weight can be assigned to every single back-end server |
47 | | - |
48 | | -## 2.Content forwarding: |
49 | | -- Filtering and blocking specific http requests and even rewriting them |
| 20 | +- Supporting reverse-proxy, 6 load-balancing algorithms in goproxy: Random, IP Hash, Round Robin, Weight Round Robin, Power of Two Choices (P2C), Consistent Hashing with Bounded Loads |
| 21 | +- Supporting GET/POST/PUT/DELETE Methods in http and CONNECT method in https in goproxy |
| 22 | +- Supporting HTTP authentication |
| 23 | +- Filtering and blocking specific http requests and even rewriting them in goproxy |
50 | 24 | - Customizing responses from third-party API |
| 25 | +- Cache support with memory or redis to speed up the responding and the expired time of caches is configurable |
| 26 | +- Flexible and eager-loading configurations |
51 | 27 |
|
52 | | -## 3.Responses can be cached in redis to speed up the responding and the expired time of caches is configurable |
53 | | - |
54 | | -## 4.Configurations are stored in a json file which is convenient for users |
55 | | - |
56 | | -# How to use goproxy |
57 | | -## 1.Get source code |
58 | | - |
59 | | ->* Clone source of goproxy from github, [goproxy](https://github.com/panjf2000/goproxy) |
60 | | ->* git clone https://github.com/panjf2000/goproxy.git |
| 28 | +## 🎉 How to use goproxy |
61 | 29 |
|
62 | | -## 2.Get those dependencies needed from goproxy: |
| 30 | +### 1.Get source code |
63 | 31 |
|
64 | | -- logrus (structured, pluggable logging for Go) |
65 | | -- ~~radix.v2 (lightweight redis client for Go)~~ |
66 | | -- redigo(Go client for Redis) |
67 | | -- cron(a *cron* library for go) |
| 32 | +```powershell |
| 33 | +go get github.com/panjf2000/goproxy |
| 34 | +``` |
68 | 35 |
|
69 | | ->Install logrus:go get github.com/Sirupsen/logrus |
| 36 | +**Besides, you also need a redis to support caching responses if you enable redis config in goproxy.** |
70 | 37 |
|
71 | | ->~~Install radix.v2:go get github.com/mediocregopher/radix.v2/…~~ |
| 38 | +### 2.Compile the source code |
72 | 39 |
|
73 | | ->Install redigo:go get github.com/gomodule/redigo/redis |
| 40 | +```powershell |
| 41 | +cd $GOPATH/src/github.com/panjf2000/goproxy |
74 | 42 |
|
75 | | -**Besides, you also need a redis to support caching responses in goproxy.** |
| 43 | +go build |
| 44 | +``` |
76 | 45 |
|
77 | | -## 3.Compile the source code |
78 | | -1. cd $GOPATH/src/github.com/panjf2000/goproxy |
79 | | -2. go build |
| 46 | +### 3.Run |
80 | 47 |
|
81 | | -## 4.Run |
82 | | -goproxy uses cfg.toml as its configurations file which is located in /etc/proxy/cfg.toml of your server, you should create a cfg.toml in there previously, here is a typical example: |
| 48 | +goproxy uses cfg.toml as its configurations file which is located in `/etc/proxy/cfg.toml` of your server, you should create a cfg.toml in there previously, here is a typical example: |
83 | 49 |
|
84 | 50 | ```toml |
85 | 51 | # toml file for goproxy |
@@ -114,41 +80,45 @@ capacity = 1000 |
114 | 80 | cache_replacement_policy = "LRU" |
115 | 81 | ``` |
116 | 82 |
|
117 | | -### configurations meaning: |
| 83 | +### Configurations: |
118 | 84 | #### [server] |
119 | | -- port:the port goroxy will listen to |
120 | | -- reverse:enable the reverse-proxy feature or not |
121 | | -- proxy_pass:back-end servers that actually provide services, like ["127.0.0.1:80^10","127.0.0.1:88^5","127.0.0.1:8088^2","127.0.0.1:8888"], weight can be assigned to every single server |
122 | | -- inverse_mode:load-balancing algoritms:0 for Randomized Algorithm; 1 for Weight Round Robin Algorithm; 2 for Power of Two Choices (P2C) Algorithm; 3 for IP Hash Algorithm; 4 for Consistent Hashing with Bounded Loads Algorithm |
123 | | -- auth:enable http authentication or not |
124 | | -- cache:enable responses caching or not |
125 | | -- cache_timeout:expired time of responses caching, in seconds |
126 | | -- cache_type: redis or memory |
127 | | -- log:log level, 1 for Debug,0 for info |
128 | | -- log_path:the path of log files |
129 | | -- user:user name from http authentication |
130 | | -- http_read_timeout:duration for waiting response from the back-end server, if goproxy don't get the response after this duration, it will throw an exception |
131 | | -- http_write_timeout:duration for back-end server writing response to goproxy, if back-end server takes a longer time than this duration to write its response into goproxy, goproxy will throw an exception |
| 85 | +- **port**:the port goroxy will listen to |
| 86 | +- **reverse**:enable the reverse-proxy feature or not |
| 87 | +- **proxy_pass**:back-end servers that actually provide services, like ["127.0.0.1:80^10","127.0.0.1:88^5","127.0.0.1:8088^2","127.0.0.1:8888"], weight can be assigned to every single server |
| 88 | +- **inverse_mode**:load-balancing algoritms:0 for Randomized Algorithm; 1 for Weight Round Robin Algorithm; 2 for Power of Two Choices (P2C) Algorithm; 3 for IP Hash Algorithm based on hash ring; 4 for Consistent Hashing with Bounded Loads Algorithm |
| 89 | +- **auth**:enable http authentication or not |
| 90 | +- **cache**:enable responses caching or not |
| 91 | +- **cache_timeout**:expired time of responses caching, in seconds |
| 92 | +- **cache_type**: redis or memory |
| 93 | +- **log**:log level, 1 for Debug,0 for info |
| 94 | +- **log_path**:the path of log files |
| 95 | +- **user**:user name from http authentication |
| 96 | +- **http_read_timeout**:duration for waiting response from the back-end server, if goproxy don't get the response after this duration, it will throw an exception |
| 97 | +- **http_write_timeout**:duration for back-end server writing response to goproxy, if back-end server takes a longer time than this duration to write its response into goproxy, goproxy will throw an exception |
132 | 98 |
|
133 | 99 | #### [redis] |
134 | | -- redis_host:redis host |
135 | | -- redis_pass:redis password |
136 | | -- max_idle:the maximum idle connections of redis connection pool |
137 | | -- idle_timeout:duration for idle redis connection to close |
138 | | -- max_active:maximum size of redis connection pool |
| 100 | +- **redis_host**:redis host |
| 101 | +- **redis_pass**:redis password |
| 102 | +- **max_idle**:the maximum idle connections of redis connection pool |
| 103 | +- **idle_timeout**:duration for idle redis connection to close |
| 104 | +- **max_active**:maximum size of redis connection pool |
139 | 105 |
|
140 | 106 | #### [mem] |
141 | 107 |
|
142 | | -- capacity: cache capacity of items |
143 | | -- cache_replacement_policy: LRU or LFU |
| 108 | +- **capacity**: cache capacity of items |
| 109 | +- **cache_replacement_policy**: LRU or LFU |
| 110 | + |
| 111 | +There should be a binary named `goproxy` as the same of project name after executing the `go build` command and that binary can be run directly to start a goproxy server. |
144 | 112 |
|
145 | | -You will get a binary file named goproxy as the same of project name after executing the `go build` command and that binary file can be run directly to start a goproxy server. |
| 113 | +The running goproxy server listens in the port set in cfg.toml and it will forward your http requests to the back-end servers set in cfg.toml by going through that port in goproxy. |
146 | 114 |
|
147 | | -The started goproxy server will listen in the port set in cfg.toml file and you can just forward your http requests to the back-end servers set in cfg.toml by going through that port in goproxy. |
| 115 | +## 🎱 Secondary development |
148 | 116 |
|
149 | | -# Secondary development |
150 | | ->Up to present, goproxy has implemented all basic functionalities like reverse-proxy, load-blancing, http caching, http requests controlling, etc and if you want to customize the responses more accurately, you can implement a new handler by inheriting (not a strict statement as there is no OO in golang) from the ProxyServer struct located in handlers/proxy.go and overriding its method named ServeHTTP, then you are allowed to write your own logic into it. |
| 117 | +Up to present, goproxy has implemented all basic functionalities like reverse-proxy, load-blancing, http caching, http requests controlling, etc and if you want to customize the responses more accurately, you can implement a new handler by inheriting (not a strict statement as there is no OO in golang) from the ProxyServer struct located in handlers/proxy.go and overriding its method named ServeHTTP, then you are allowed to write your own logic into it. |
151 | 118 |
|
152 | | -# Thanks |
| 119 | +## 🙏🏻 Thanks |
153 | 120 |
|
154 | | -[httpproxy](https://github.com/sakeven/httpproxy) |
| 121 | +- [httpproxy](https://github.com/sakeven/httpproxy) |
| 122 | +- [gcache](https://github.com/bluele/gcache) |
| 123 | +- [viper](https://github.com/spf13/viper) |
| 124 | +- [redigo](https://github.com/gomodule/redigo) |
0 commit comments