-
Notifications
You must be signed in to change notification settings - Fork 0
Vulnerability Disclosure Tiers
Vulnerability disclosure often happens in a cascading manner - from one person who discovers it to the public Internet. While everyone agrees that vulnerabilities need to be eventually disclosed in some form, (1) content (2) audience and (3) timing (C A T) of disclosure is often a topic of contention and discontent. There is a hope that if we take out subjectivity from disclosure C A T, vulnerability disclosures can be less painful, especially for critical vulnerabilities.
Audience should be selected based on their role, and if they play by the rules of disclosure. It may not matter if they work for the same organization or not. Same individuals/teams may perform two or three roles. An incident responder may identify the audience and facilitate the flow the contents between tiers.
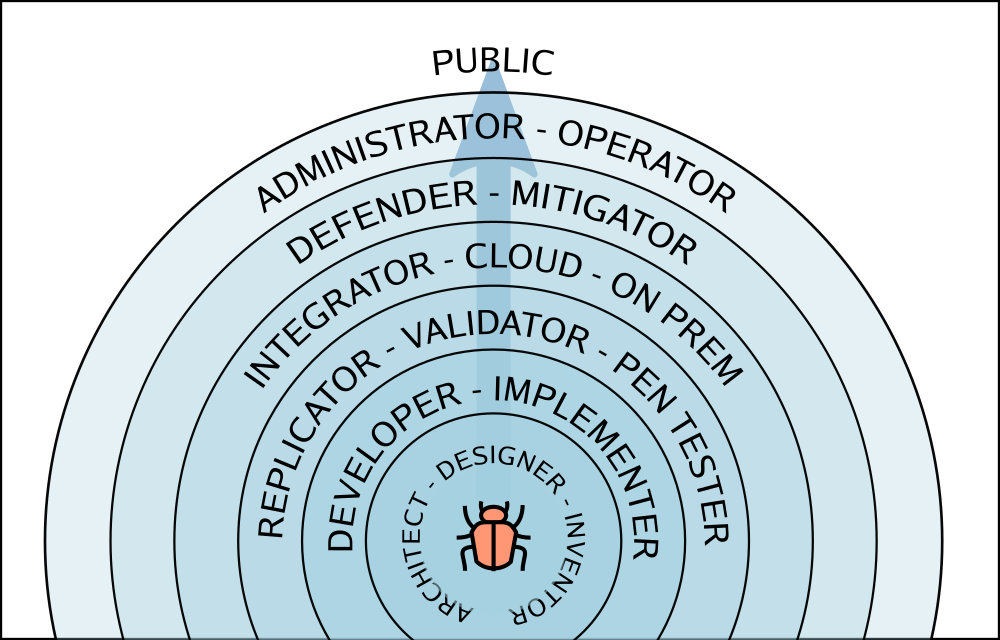
Content: Nothing → vulnerability report, PoC (Proof of Concept)
Content: vulnerability report, PoC → well defined problem statement, root cause, solutions, PoC
Content: problem, root cause, solutions, PoC → problem, root cause, solutions, PoC, fix
Content: problem, root cause, solution, PoC, fix → problem, solution, fix, recurrence prevention, conformance tests, workarounds, attack vectors
Tier 4 - integrators, large could/service operators, managed products, managed on premises deployments
Content: problem, risk, solution, fix, workarounds → feedback
Content: problem, attack vectors → problem, attack vectors, detection, prevention
Content: problem, risk, solution, fix, workarounds → feedback
Content: problem, attack vectors, risk, solution, fix, workarounds, detection, prevention.