Conversation
|
I tried using this example, and added a few keys: However, this results in an error on startup: |
|
Error is now: |
|
I've confirmed locally that Helidon 3 only works with Java 17+. |
|
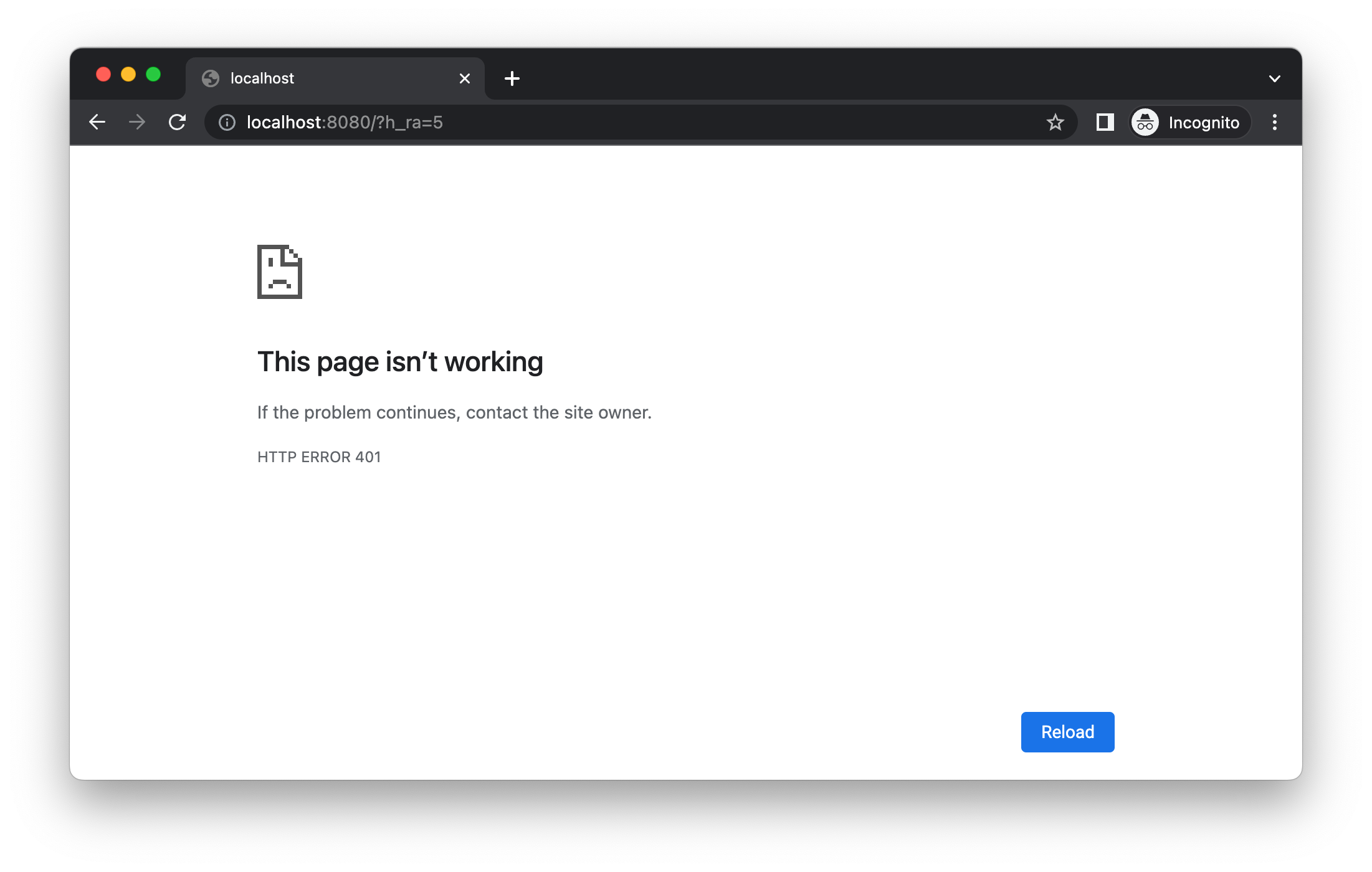
@tomas-langer I'm still unable to get OIDC working with Helidon 3. If I start the app and go to http://localhost:8080, it does redirect me to Okta. However, when it comes back to the app, it gives me a 401 in my browser. |
|
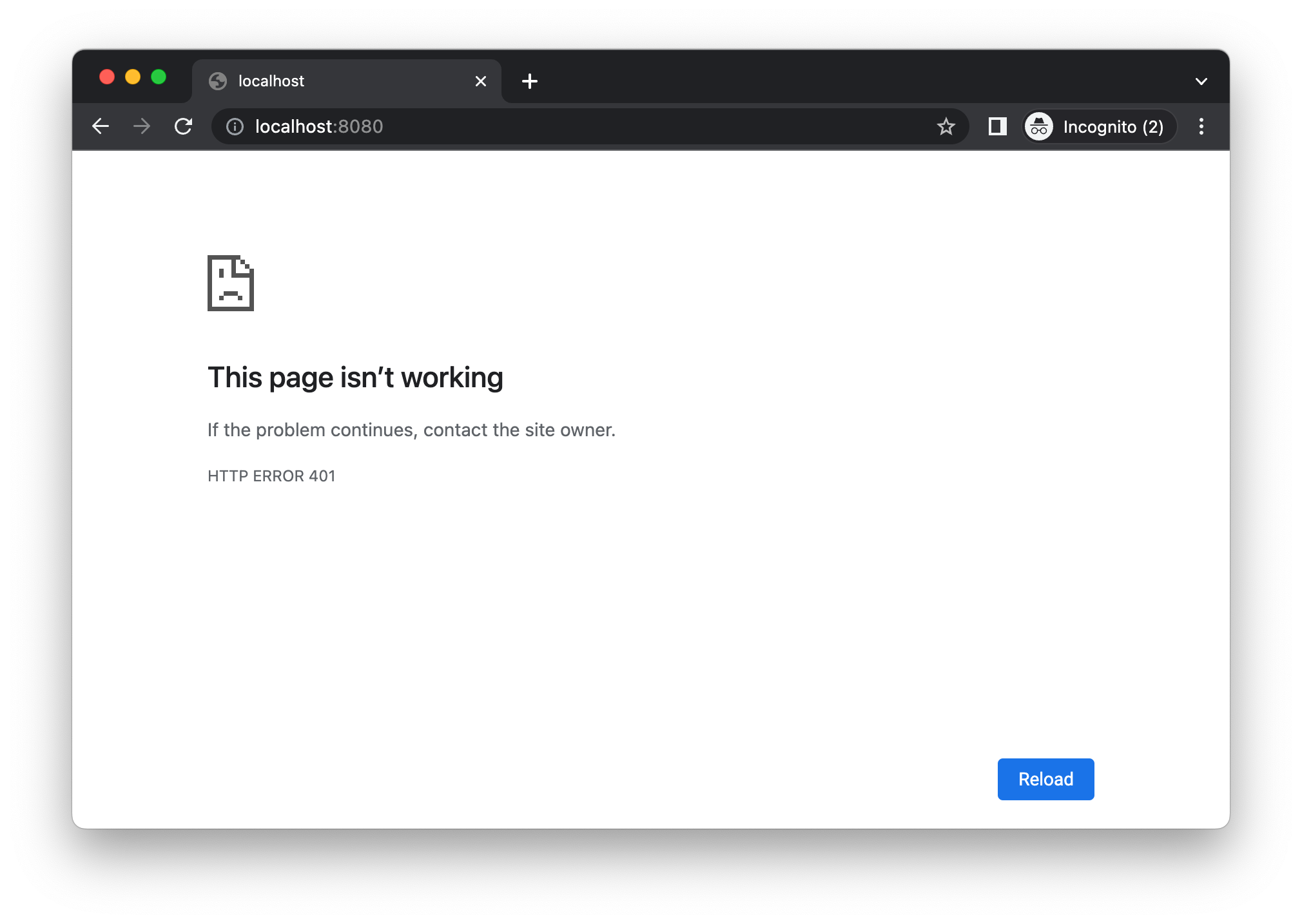
I tried upgrading to Helidon 3.0.1 and now I get a 401 when I launch http://localhost:8080. |
|
@tomas-langer I tested this again today with the latest bits. Hitting If I try hitting The default audience for Okta dev accounts is |
No description provided.