-
-
Notifications
You must be signed in to change notification settings - Fork 310
Data Analysis in AppControl Manager
AppControl Manager can now analyze the App Control for Business (Code Integrity) and AppLocker data from Event Logs or Microsoft Defender for Endpoint (MDE) Advanced Hunting. This feature is available in the Event Logs Policy Creation and MDE Advanced Hunting pages. All of the data are localized so you can change the language in the app's settings page in order to view the data in your own language.
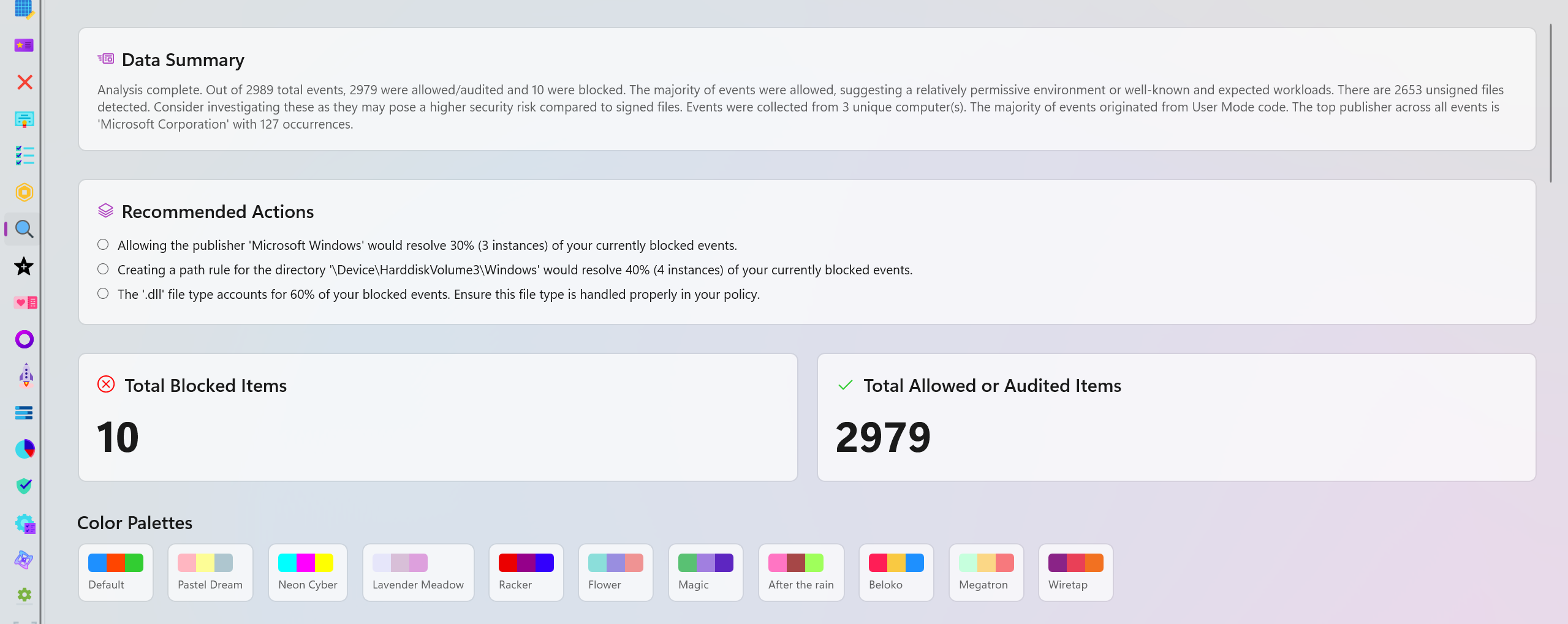
A brief overview of the available data and what they mean. It points out edge cases, provides easy to understand comparison of different data points and explains how the data is distributed in different categories.
This section will provide you with one or more recommendations based on your data. For instance, it can suggest specific policies to be deployed to resolve blocked items or recommend you to review certain parts of the logs because an excessive amount of blocked or audited events were detected in a short period of time.
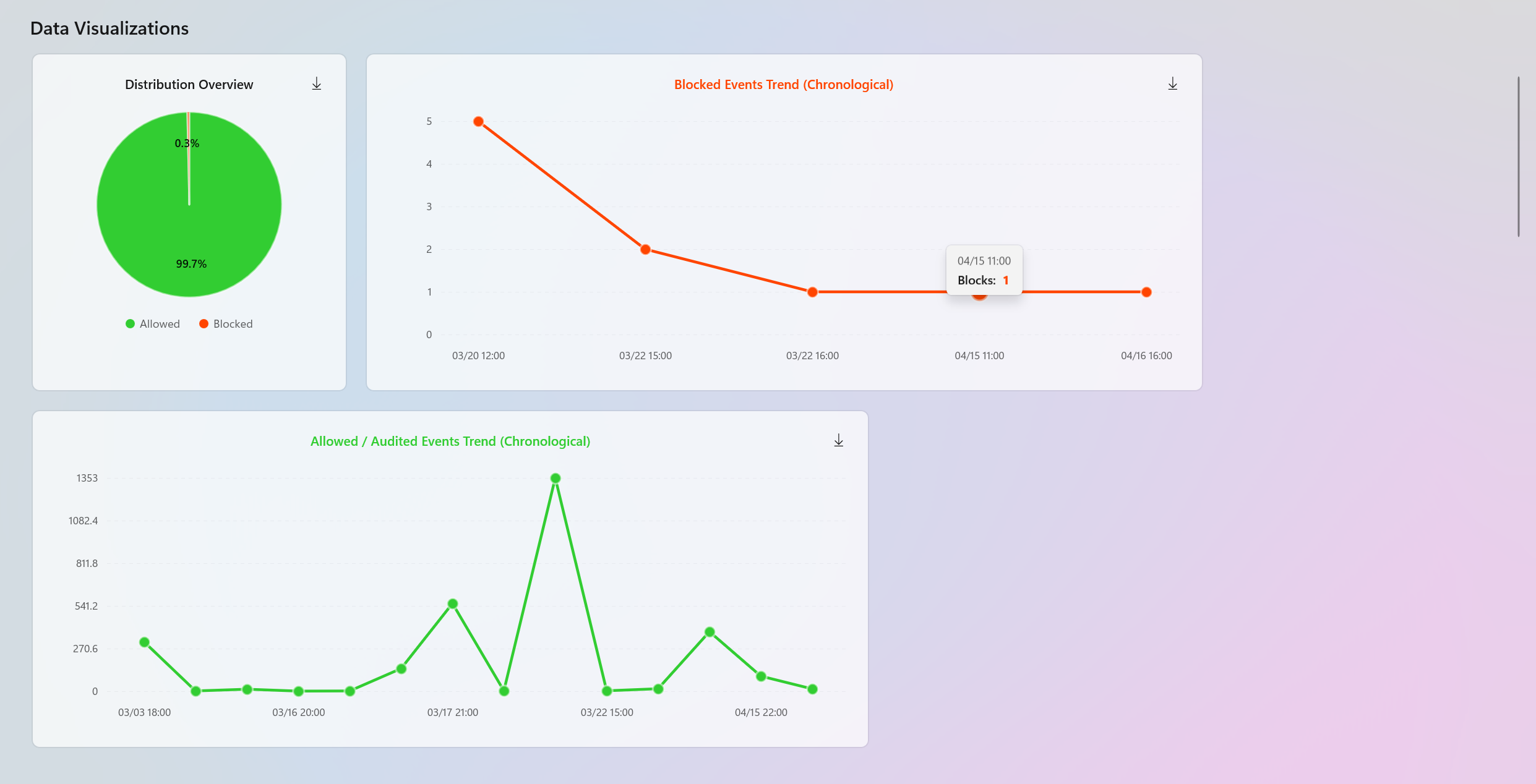
Interactive charts are dynamically generated to help with data visualization. You will have access to the entire blocked and audited/allowed trends in chronological order to quickly identify the peak points and detect anomalies. These charts have HotSpots where you can hover over or click to view additional information about specific points in time. You can also download these charts on your system as SVG files.
There is also a Pie chart displaying the distribution overview of the entire data set.
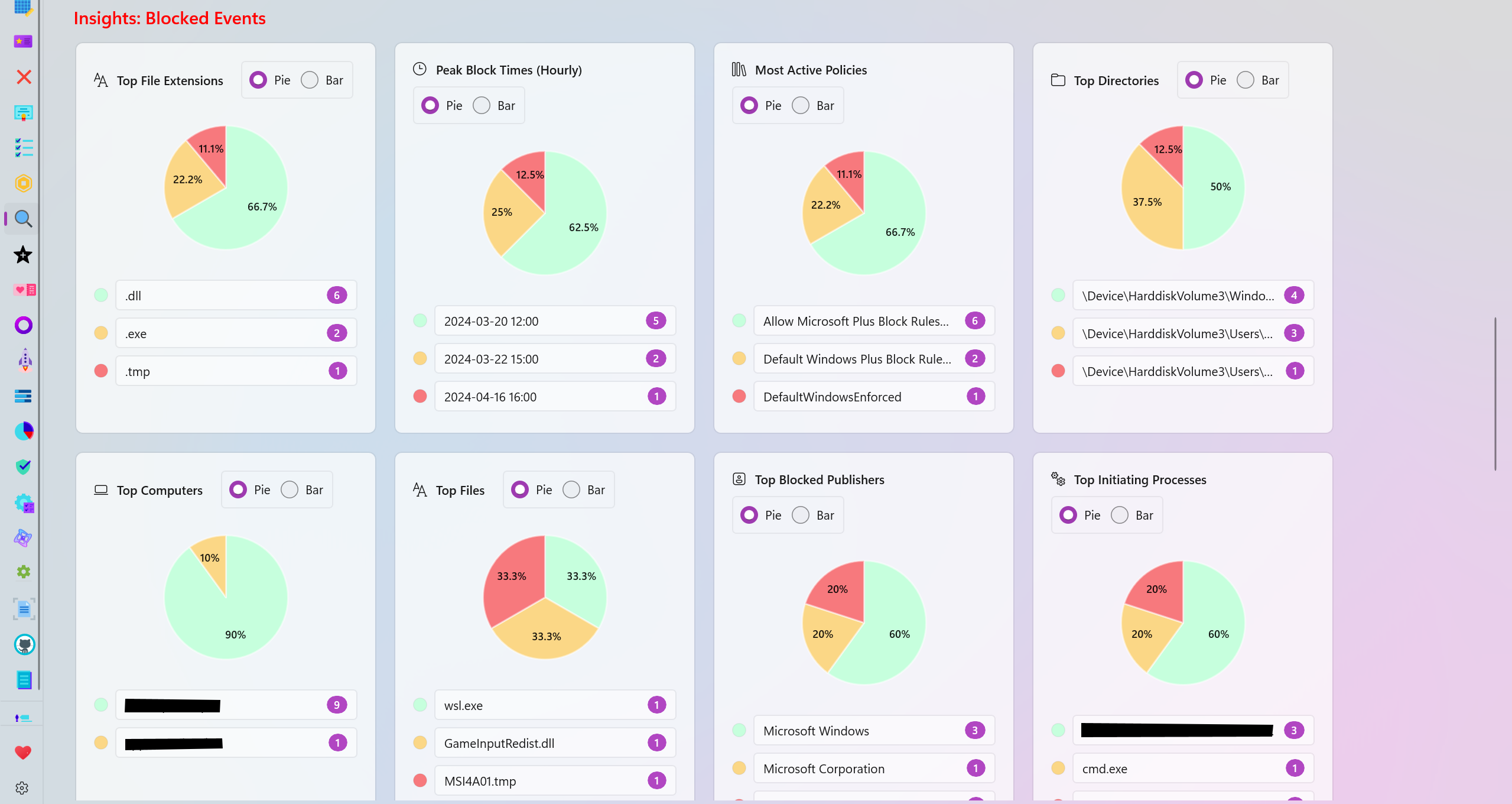
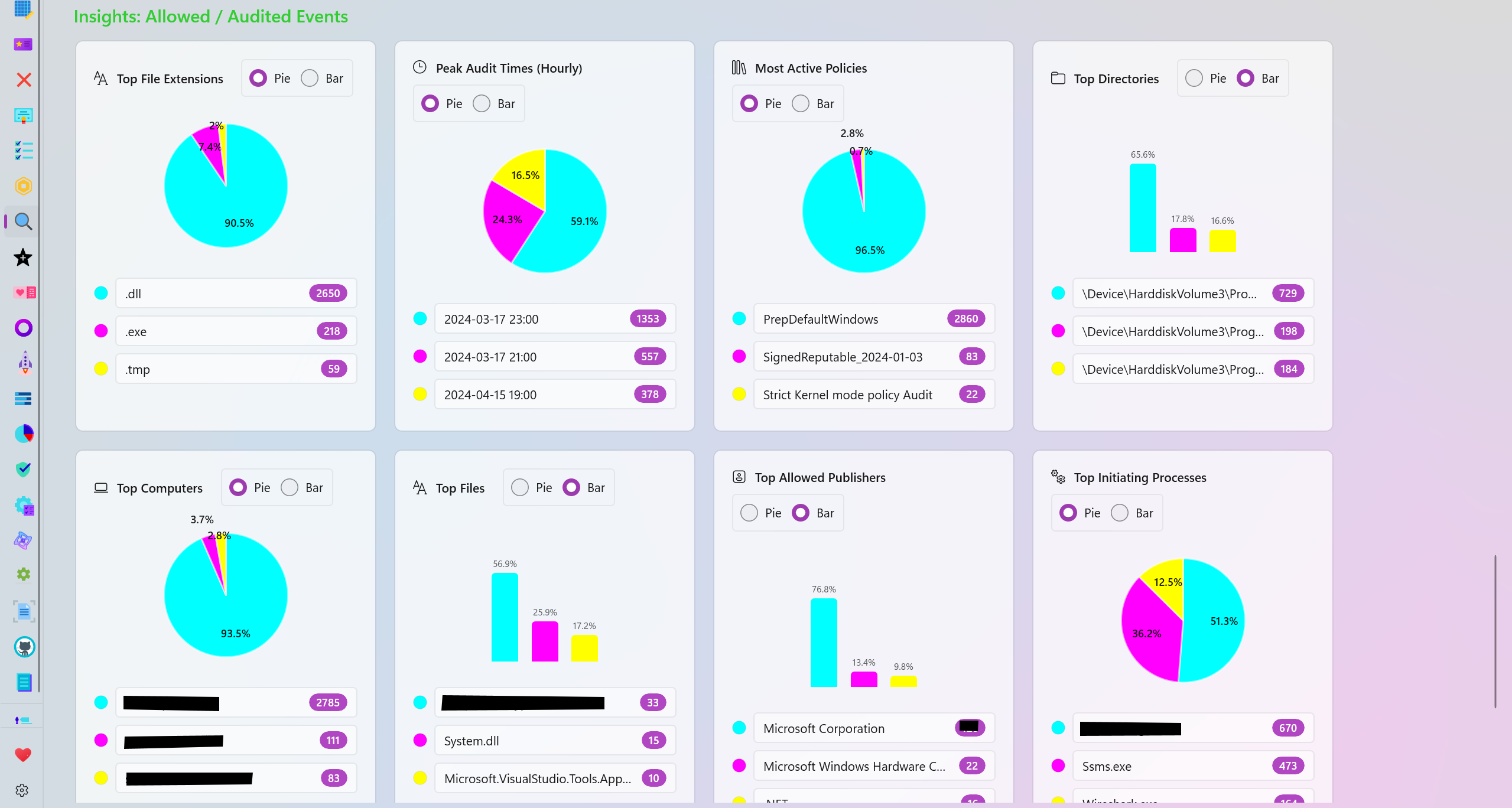
The analysis page generates many categories based on your data for further visualization of the blocked or allowed/audited data.
- Top File Extensions: View the top file extensions that were blocked or audited.
- Peak Block/Audit Times (Hourly): View the time frames where the most blocked or audited logs were generated.
- Most Active Policies: View the top most active policies responsible for generating the most blocked or audited logs.
- Top Directories: View the top directories where the most audited or blocked logs originate from.
- Top Computers: View the names of the top computers/systems that generated the most blocked or audited logs.
- Top Files: View the names of the top files that were blocked or audited the most.
- Top Publishers: View the names of the top file/program publishers that were audited or blocked the most.
- Top Initiating Processes: View the names of the processes that the most blocked or audited logs were initiated from.
- Top packaged Apps: View the top Package Family Names (PFNs) that were blocked or audited.
- Signing Scenario: View the distribution overview of the Signed vs Unsigned files among the blocked or audited logs.
There are multiple color palettes to choose from in order to personalize the charts available in the analysis page. Each slice of a pie or each part of a bar chart can also be individually colorized to meet your needs.
If you have any feedback or suggestions, please don't hesitate to create a new issue or discussion on this GitHub repository.
- Create AppControl Policy
- Create Supplemental Policy
- System Information
- Configure Policy Rule Options
- Policy Editor
- Simulation
- Allow New Apps
- Build New Certificate
- Create Policy From Event Logs
- Create Policy From MDE Advanced Hunting
- Create Deny Policy
- Merge App Control Policies
- Deploy App Control Policy
- Get Code Integrity Hashes
- Get Secure Policy Settings
- Update
- Sidebar
- Validate Policies
- View File Certificates
- Microsoft Graph
- Firewall Sentinel
- Data Analysis in AppControl Manager
- Protect
- Microsoft Security Baselines
- Microsoft Security Baselines Overrides
- Microsoft 365 Apps Security Baseline
- Microsoft Defender
- Attack Surface Reduction
- Bitlocker
- Device Guard
- TLS Security
- Lock Screen
- User Account Control
- Windows Firewall
- Optional Windows Features
- Windows Networking
- Miscellaneous Configurations
- Windows Update
- Edge Browser
- Certificate Checking
- Country IP Blocking
- Non Admin Measures
- Group Policy Editor
- Manage Installed Apps
- File Reputation
- Audit Policies
- Cryptographic Bill of Materials
- Intune
- Configuration Service Provider (CSP)
- Service Manager
- Duplicate Photos Finder
- EXIF Manager
- Bootable Drive Maker
- Introduction
- How To Generate Audit Logs via App Control Policies
- How To Create an App Control Supplemental Policy
- The Strength of Signed App Control Policies
- How To Upload App Control Policies To Intune Using AppControl Manager
- How To Create and Maintain Strict Kernel‐Mode App Control Policy
- How to Create an App Control Deny Policy
- App Control Notes
- How to use Windows Server to Create App Control Code Signing Certificate
- Fast and Automatic Microsoft Recommended Driver Block Rules updates
- App Control policy for BYOVD Kernel mode only protection
- EKUs in App Control for Business Policies
- App Control Rule Levels Comparison and Guide
- Script Enforcement and PowerShell Constrained Language Mode in App Control Policies
- How to Use Microsoft Defender for Endpoint Advanced Hunting With App Control
- App Control Frequently Asked Questions (FAQs)
- System Integrity Policy Transformations | XML to CIP and Back
- About Code Integrity Policy Signing
- How To Install Microsoft Store Apps Completely Offline
- Create Bootable USB flash drive with no 3rd party tools
- Event Viewer
- Group Policy
- How to compact your OS and free up extra space
- Hyper V
- Git GitHub Desktop and Mandatory ASLR
- Signed and Verified commits with GitHub desktop
- About TLS, DNS, Encryption and OPSEC concepts
- Things to do when clean installing Windows
- Comparison of security benchmarks
- BitLocker, TPM and Pluton | What Are They and How Do They Work
- How to Detect Changes in User and Local Machine Certificate Stores in Real Time Using PowerShell
- Cloning Personal and Enterprise Repositories Using GitHub Desktop
- Only a Small Portion of The Windows OS Security Apparatus
- Rethinking Trust: Advanced Security Measures for High‐Stakes Systems
- Clean Source principle, Azure and Privileged Access Workstations
- How to Securely Connect to Azure VMs and Use RDP
- Basic PowerShell tricks and notes
- Basic PowerShell tricks and notes Part 2
- Basic PowerShell tricks and notes Part 3
- Basic PowerShell tricks and notes Part 4
- Basic PowerShell tricks and notes Part 5
- How To Access All Stream Outputs From Thread Jobs In PowerShell In Real Time
- PowerShell Best Practices To Follow When Coding
- How To Asynchronously Access All Stream Outputs From Background Jobs In PowerShell
- Powershell Dynamic Parameters and How to Add Them to the Get‐Help Syntax
- RunSpaces In PowerShell
- How To Use Reflection And Prevent Using Internal & Private C# Methods in PowerShell
