-
Notifications
You must be signed in to change notification settings - Fork 264
7. GitHub Secret Hunting
“samuele edited this page Feb 21, 2026
·
1 revision
RedAmon includes a GitHub Secret Hunter module that searches GitHub repositories for exposed secrets, API keys, and credentials related to your target. It runs as an independent module (separate from the recon pipeline), triggered from the Graph Dashboard toolbar.
The scanner uses 40+ regex patterns and Shannon entropy analysis to detect:
- AWS access keys and secret keys
- Google Cloud credentials and service account keys
- Database connection strings (MongoDB, PostgreSQL, MySQL, Redis)
- JWT tokens and session secrets
- Private RSA/SSH keys
- Slack, Discord, Stripe, Twilio, Sendgrid tokens
- Generic API keys and passwords in code
- And many more credential patterns
The scanner requires a Personal Access Token (PAT) for API access. The token is used exclusively for read-only scanning — it never creates, modifies, or deletes anything on GitHub.
- Go to GitHub.com and click your profile picture (top-right) then Settings
- In the left sidebar, scroll down and click Developer settings
- Click Personal access tokens then Tokens (classic)
- Click Generate new token then Generate new token (classic)
- Give it a descriptive name (e.g.,
redamon-secret-scan) - Set an expiration (recommended: 30 or 90 days)
- Select these scopes:
| Scope | Required? | Purpose |
|---|---|---|
repo |
Yes | Read repository contents and search code |
read:org |
If scanning orgs | List organization repositories and members |
gist |
If scanning gists | Access public and private gists |
- Click Generate token and copy the token immediately (starts with
ghp_). You won't see it again.
- Go to your project settings (Projects page > click project card)
- Navigate to the Integrations tab (Tab 9)
- Enter your settings:
| Field | Description |
|---|---|
| GitHub Access Token | Paste your ghp_... token. All other fields are disabled until this is set |
| Target Organization | The GitHub org name or username to scan (e.g., example-inc or johndoe) |
| Target Repositories | Comma-separated repo names to limit scope (e.g., webapp, api-server). Leave empty to scan all |
| Scan Member Repositories | Also scan repos of individual org members (significantly increases scope) |
| Scan Gists | Search gists for leaked secrets |
| Scan Commits | Examine commit history (catches secrets committed and later removed). Most expensive — disabling saves 50%+ time |
| Max Commits to Scan | Maximum commits per repo (default: 100). Scales linearly: 500 = ~5x time |
| Output as JSON | Save complete results as a downloadable JSON file |
- Click Save
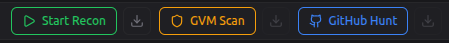
- On the Graph Dashboard, locate the GitHub Secret Hunt group (orange, GitHub icon) in the toolbar
- Click the "GitHub Hunt" button
- Click the Logs button to watch real-time progress
- When complete, click the Download button to save results as JSON
GitHub Hunt findings are stored in the Neo4j graph:
- GithubHunt → Repository → Secret / SensitiveFile nodes
- Each secret includes: file path, line number, matched pattern name, entropy score, and the matched content
The AI agent can access these findings through graph queries and incorporate them into its attack analysis.
| Parameter | Default | Description |
|---|---|---|
| GitHub Access Token | — | PAT for GitHub API access (ghp_...) |
| Target Organization | — | GitHub org or username to scan |
| Target Repositories | (all) | Comma-separated repo names to limit scope |
| Scan Member Repositories | false | Include individual member repos |
| Scan Gists | false | Search gists for secrets |
| Scan Commits | false | Examine git history for removed secrets |
| Max Commits to Scan | 100 | Max commits per repo (1-1000) |
| Output as JSON | false | Save results as downloadable JSON |
- AI Agent Guide — use the AI agent to analyze all findings including leaked secrets
User Guide
- Getting Started
- User Management
- Creating a Project
- The Graph Dashboard
- Running Reconnaissance
- GVM Vulnerability Scanning
- GitHub Secret Hunting
- AI Agent Guide
- CypherFix — Automated Remediation
Reference
- Project Settings Reference
- AI Model Providers
- Attack Surface Graph
- Data Export & Import
- EvoGraph — Attack Chain Evolution
- Attack Paths
Help